"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."

Cyber Insurance is a form of insurance for businesses and individuals against Internet-based threats....
Read more
Digital Content Management (DCM) is the process for collection, delivery, retrieval, governance...
Read more
Cyberwarfare is the use of sophisticated cyber weapons (viruses, worms, trojans, etc.) by one...
Read more
An Application Programming Interface (API) is a set of definitions and protocols for building...
Read more
The Tor Browser is a web browser designed for anonymous web browsing and protection against traffic...
Read more
Digital Rights Management (DRM) are measures taken to protect digital media copyrights. DRM tries to...
Read more
A Data Spill, or Data Leak, is the accidental or deliberate exposure of information into an...
Read more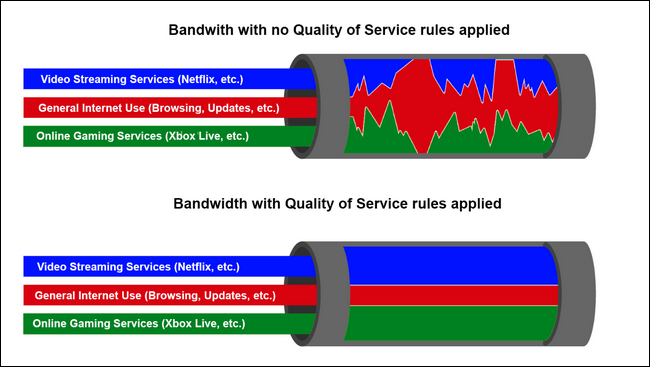
Quality of Service (QoS) is a technology that manages and prioritizes certain types of data traffic on...
Read more
Network Behavior Analysis (NBA), also known as "Behavior Monitoring" is the collection and analysis of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
