"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."
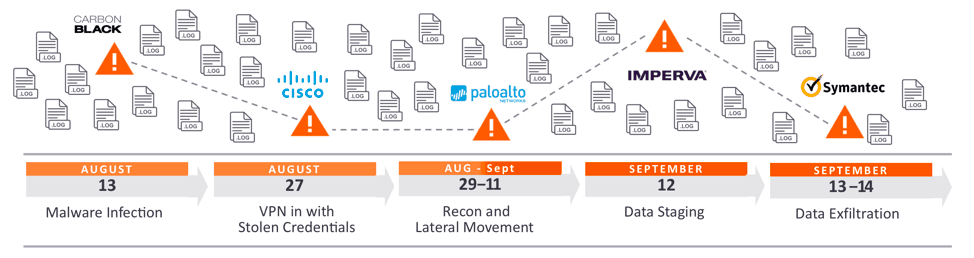
Lateral Movement is the technique that hackers use after gaining initial access to machines or...
Read more
Reconnaissance in cybersecurity refers to the preliminary step of a cyberattack, where a hacker is...
Read more
A Secure Web Gateway (SWG) is a tool that shields users from web-based threats as well as applying and...
Read more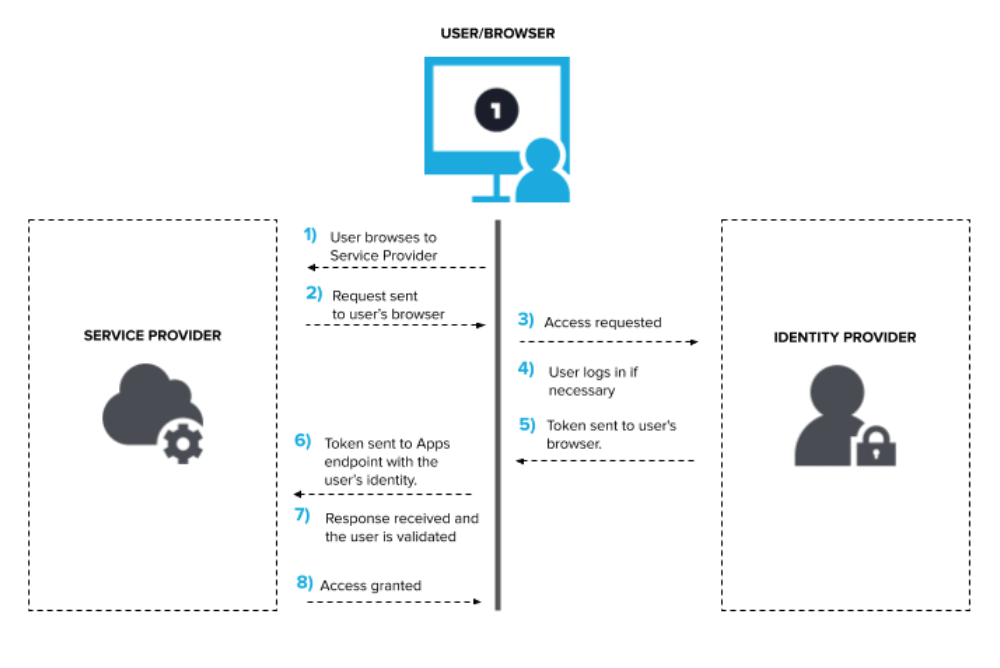
Single Sign-On (SSO) is an authentication method that enables users to securely authenticate with multiple...
Read more
A PDF (Portable Document Format) is a file format designed to present documents consistently across...
Read more
A Malicious URL is a link created with the purpose of promoting scams, attacks, and fraud. By clicking...
Read more
SSAE Compliance, also known as Statement on Standards for Attestation Engagements and Compliance, is a...
Read more
All-Source Analysis is the analysis of threat information from multiple sources, disciplines, and...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
