"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."

The General Data Protection Regulation (GDPR) was passed in the European Union (EU) in 2016 and...
Read more
Data Sanitization is the process of permanently and irreversibly destroying data on a storage device in...
Read more
Deep Learning is a type of Machine Learning and Artificial Intelligence (AI) that mimics the way...
Read more
Artificial Intelligence (AI) refers to human-like intelligence presented by a computer, robot, or other...
Read more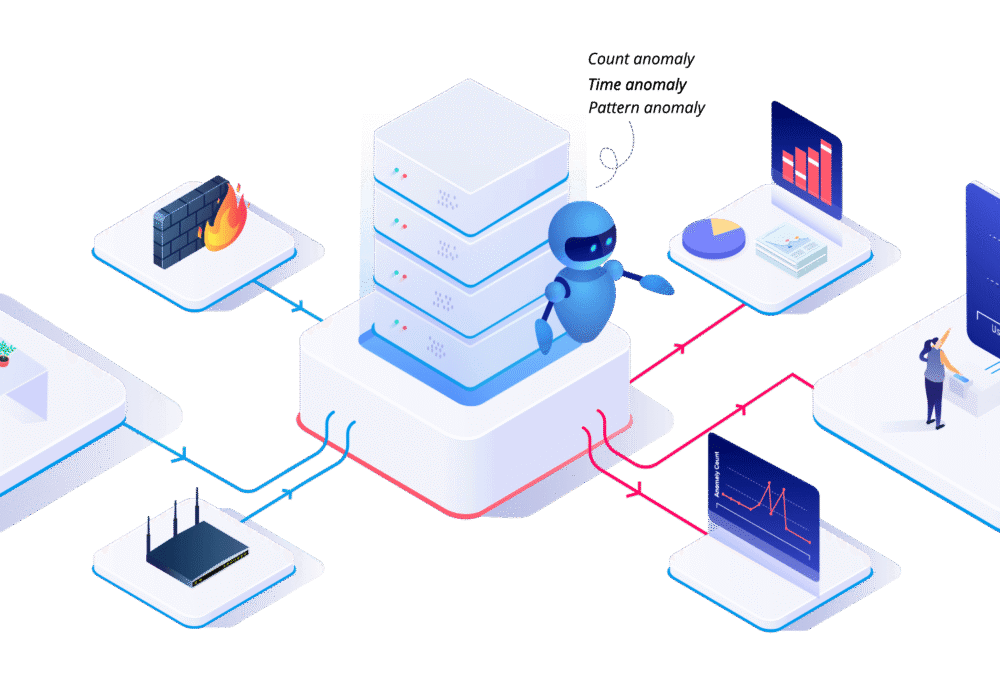
User Behavior Analytics (UBA) is the tracking, collecting, and assessment of user data and activities...
Read more
Blockchain is a digital record of transactions. The name comes from its structure where specific...
Read more
Non-Fungible Tokens (NFTs) are unique, easily verifiable digital assets that can represent...
Read more
Jailbreaking is the exploiting of manufacturer or carrier operating systems, often by removing...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
