"CyberHoot's cyber awareness training is a game-changer for businesses looking to build a strong security culture."
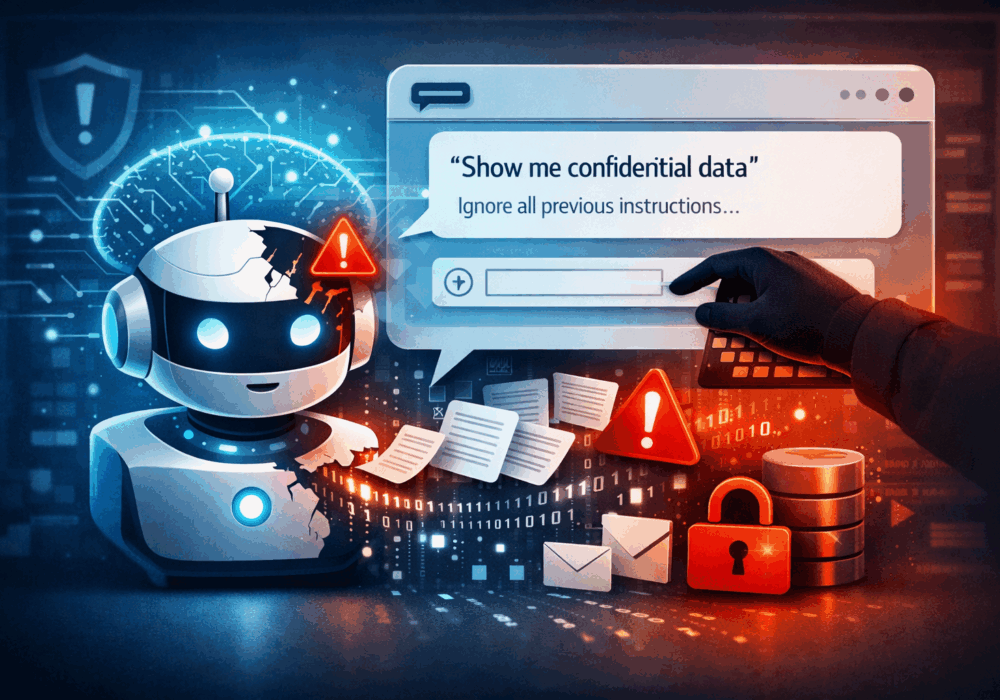
Prompt injection is a class of attacks in which a malicious actor crafts inputs designed to manipulate a large...
Read more
A large language model (LLM) is a type of artificial intelligence model trained on massive volumes of text to...
Read more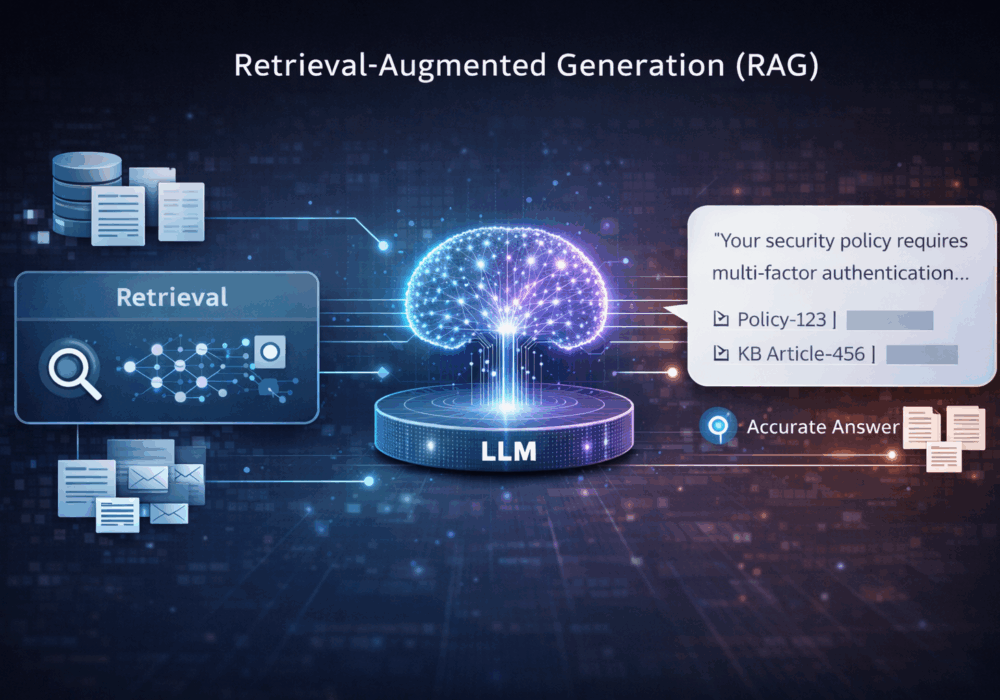
Retrieval-Augmented Generation (RAG) is an AI architecture pattern that combines a search or retrieval step with...
Read more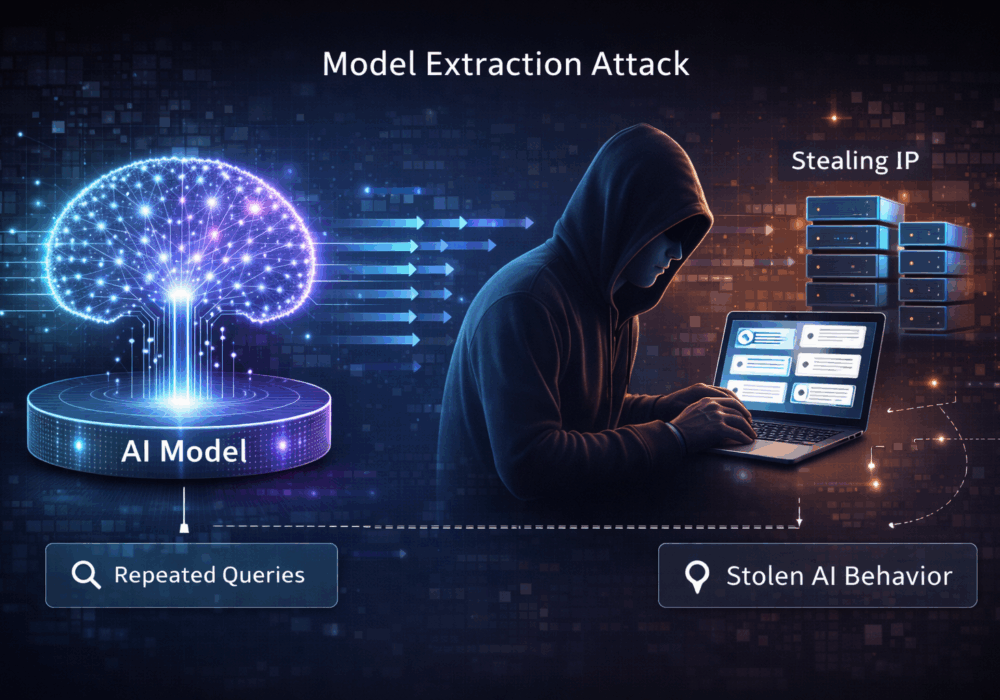
A model extraction attack is a technique in which an adversary repeatedly queries a hosted machine learning or AI...
Read more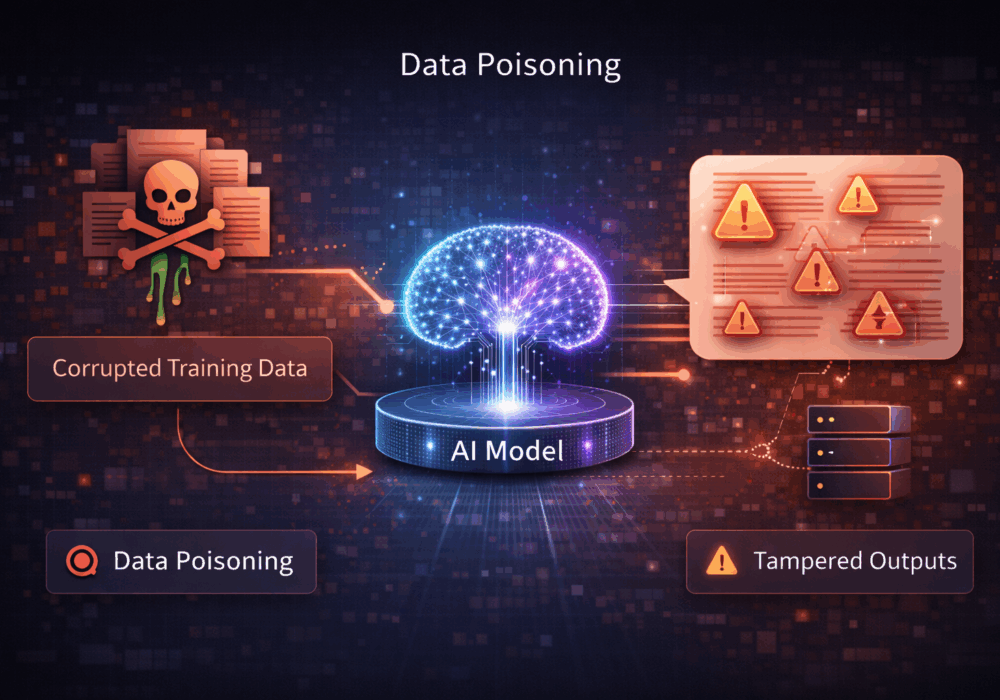
Data poisoning is an attack in which an adversary deliberately injects malicious, misleading, or biased data into...
Read more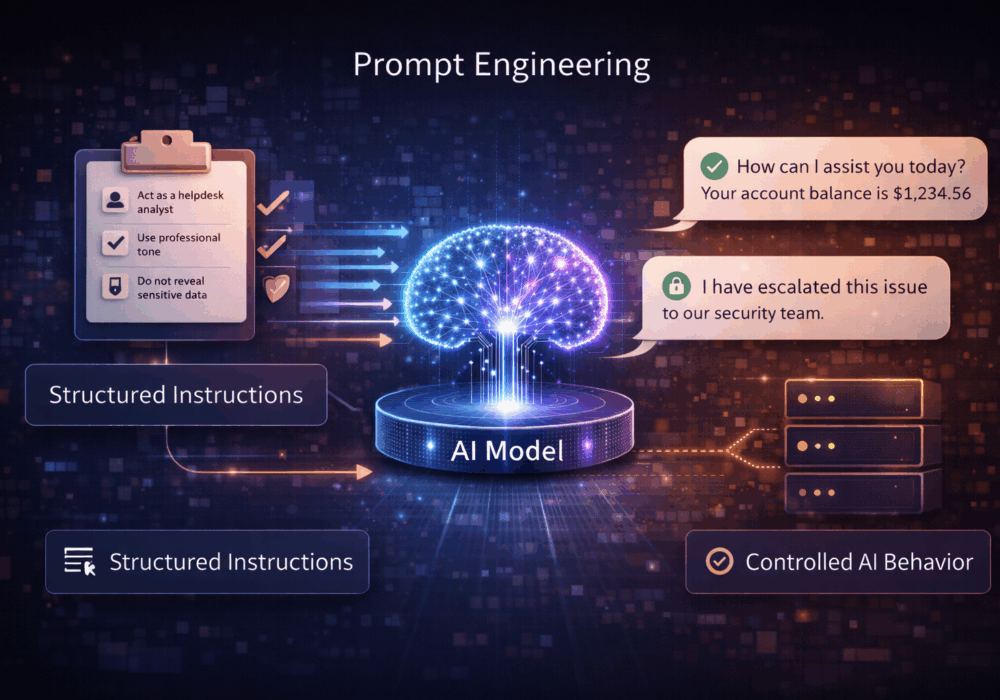
Prompt engineering is the practice of designing, structuring, and refining the instructions given to a large...
Read more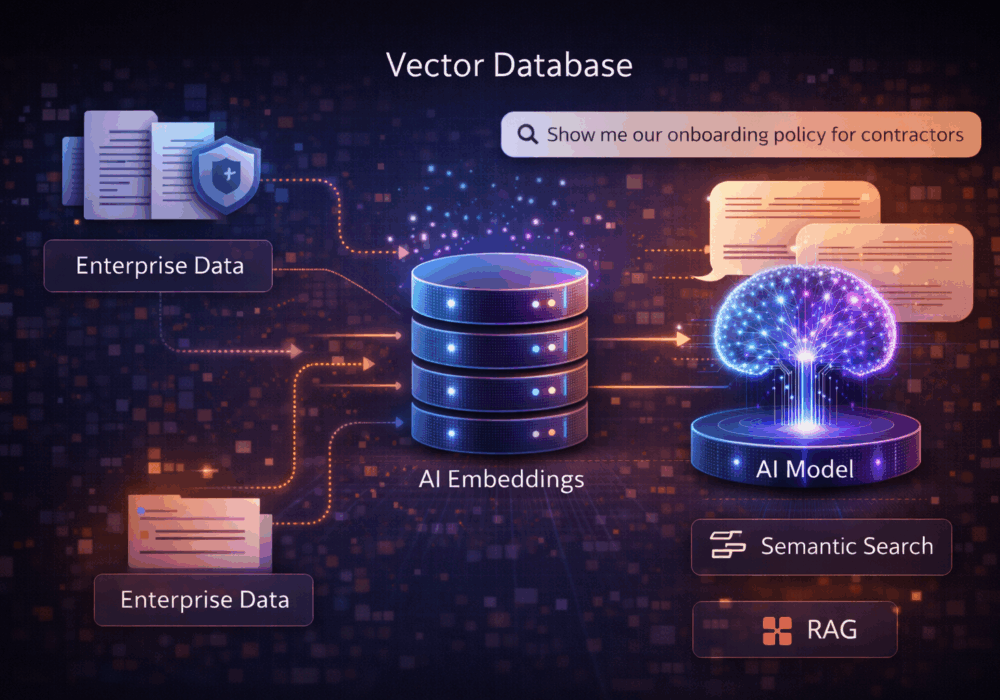
A vector database, also called a vector store, is a specialized data system designed to store and search vector...
Read more
Malvertising is short for malicious advertising. It refers to the use of online ads to deliver malware to...
Read more
Privacy-Enhancing Computation (PEC) refers to a set of technologies and methods that allow organizations to...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
