"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."

Image Source An Industrial Control System is an information system used to control industrial...
Read more
Supervisory Control and Data Acquisition Supervisory Control and Data Acquisition (SCADA) is a generic name...
Read more
A Supply Chain is a system of organizations, people, activities, information and resources, for creating and...
Read more
Image Source Supply Chain Risk Management refers to the process of identifying, analyzing, and assessing...
Read more
Risk Reduction (limitation) is the most common risk management strategy used by businesses. This...
Read more
Image Source Risk Acceptance (Accept) refers to accepting the risk that is presented to you or your...
Read more
Image Source Avoidance refers to avoiding the risk that is found altogether. When mitigating risk, there are...
Read more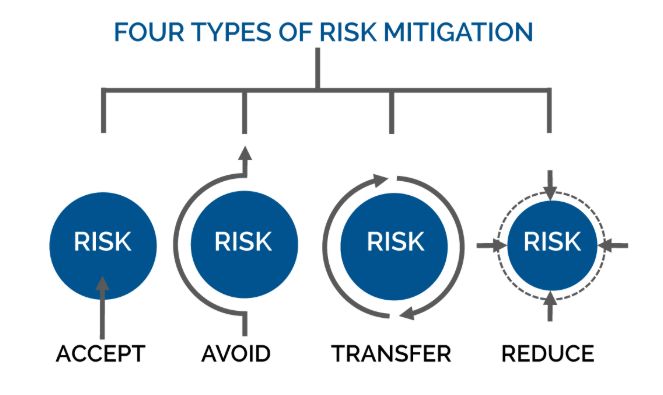
Image Source Mitigation occurs when assessing risk. When assessing risk there are many ways to work...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
