"CyberHoot is an excellent cybersecurity training platform that educates teams on security practices through training content, phishing simulations, and actionable analytics."
A Block List or Deny List, (deprecated: Blacklist), is a list of entities that are blocked or...
Read more
Image Source Active content is software that is able to automatically carry out or trigger actions without...
Read more
Decryption is the process of transforming ciphertext into its original plaintext. This is done...
Read more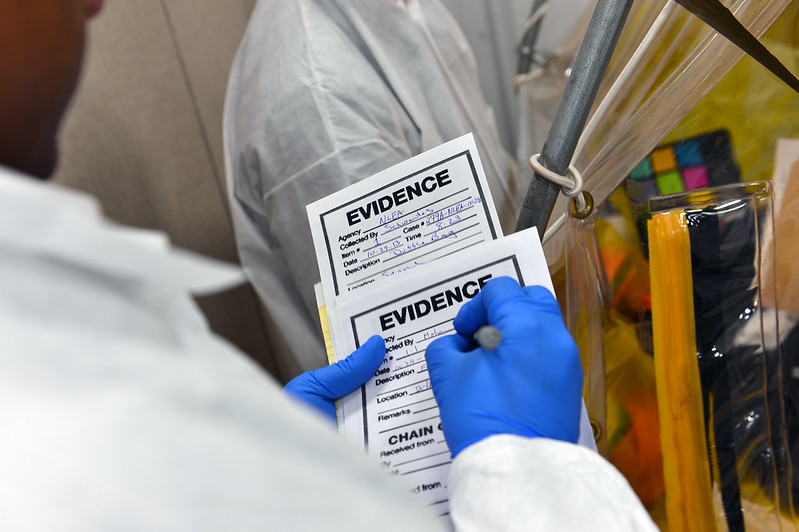
Image Source Digital Forensics is the processes and specialized techniques for gathering, retaining, and...
Read more
Cyber Criminals are individuals or teams of people who use technology to commit malicious...
Read more
Image Source In the NICE Workforce Framework, Education and Training in cybersecurity work is where a person...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
