"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”

Security Operations refers to the actions that go on within a Security Operations Center. Those within...
Read more
Image Source Cloud Computing is a model for enabling on-demand network access to a shared pool of...
Read more
Computer Network Defense is the actions taken to defend against unauthorized activity within computer...
Read more
Authentication is the process of verifying the identity or other attributes of an...
Read more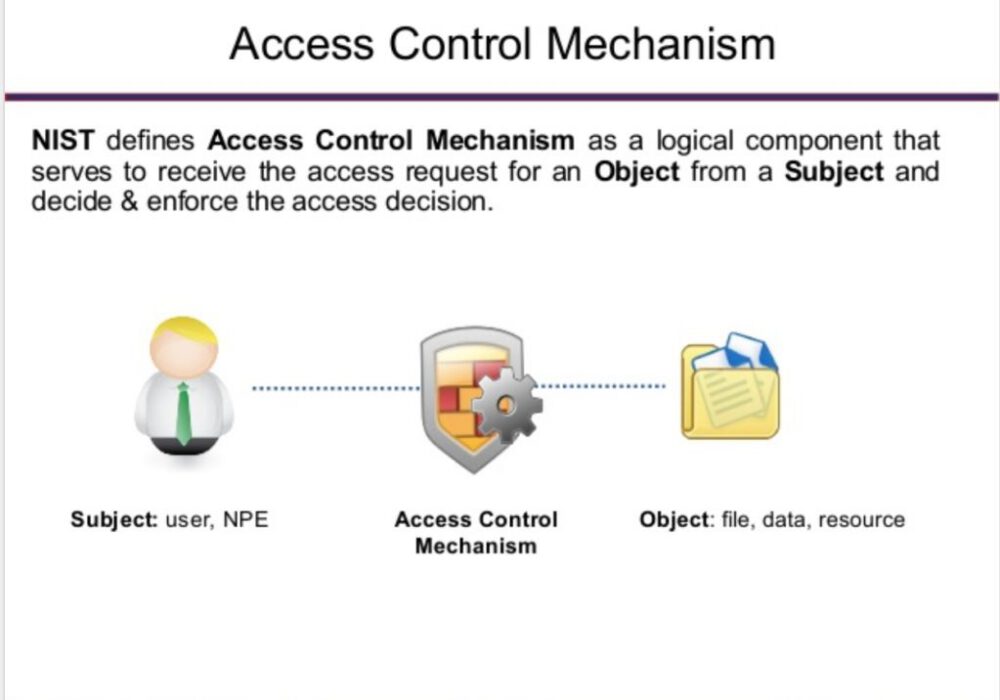
Image Source An access control mechanism is a security safeguard (i.e., hardware and software...
Read more
A Block List or Deny List, (deprecated: Blacklist), is a list of entities that are blocked or...
Read more
Image Source Active content is software that is able to automatically carry out or trigger actions without...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
