"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."
A Blended Threat is a computer network attack that seeks to maximize the severity of damage and speed...
Read more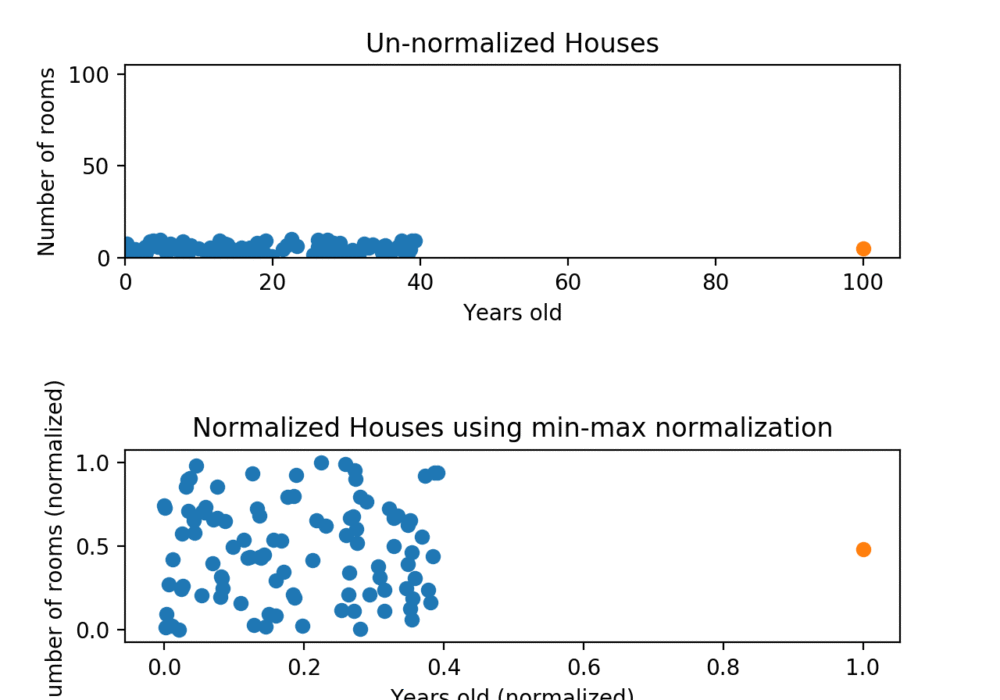
Data Normalization is a process of reorganizing information in a database to meet two...
Read more
Catfishing is a common technique used on social media sites to attack victims through fake...
Read more
Updated: 9/9/2024 with new links to Freeze your Credit.Identity Theft is when a hacker uses your...
Read more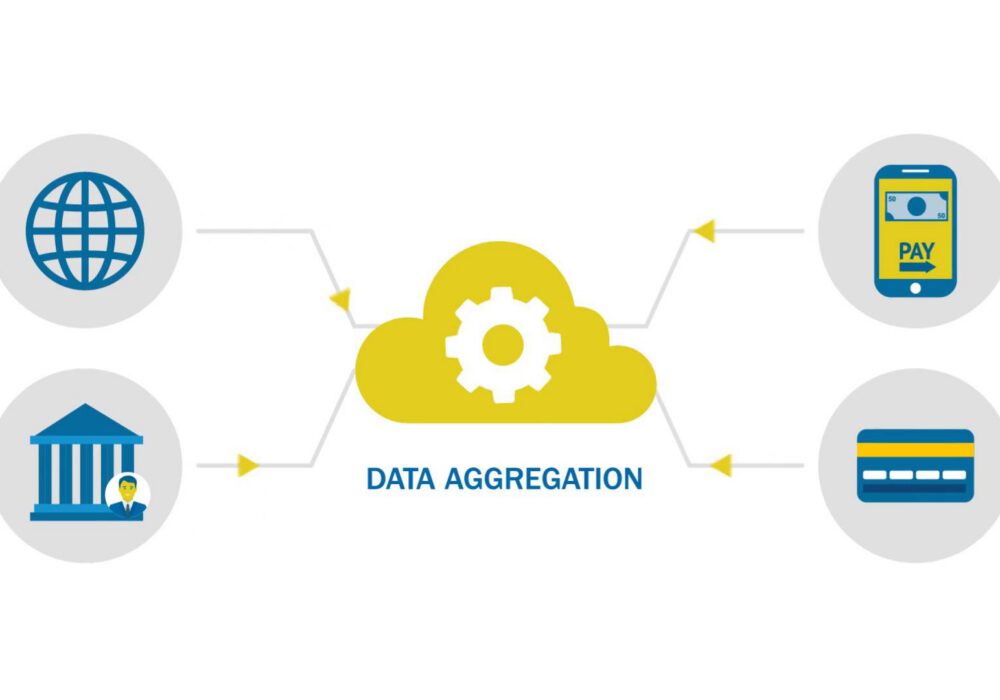
Data Aggregation is any process where data is gathered and expressed in a summary form. Data...
Read more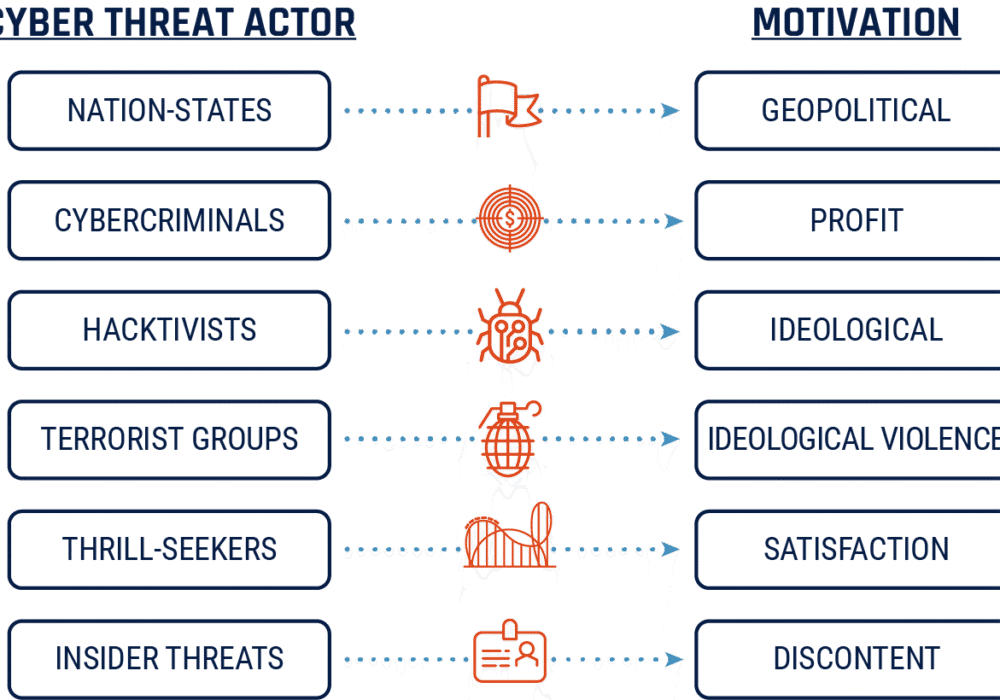
A Threat Actor is a person or group performing malicious or hostile actions which cause harm to the...
Read more
JavaScript is a programming language developed by Netscape commonly used in web development; used to...
Read more
Cyberspace is the complex environment of interdependent networks of IT infrastructures including the...
Read more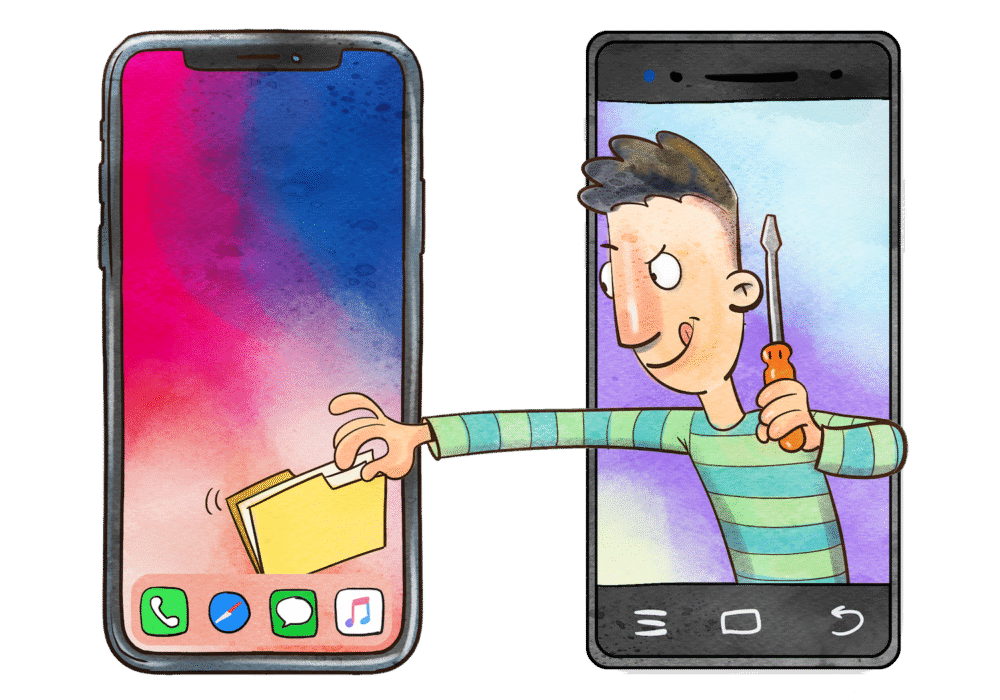
JBOH (JavaScript-Binding-Over-HTTP) is a mobile device attack that enables an attacker to...
Read more
Situational awareness is knowledge combined with attitudes and behaviors that work to protect our IT...
Read more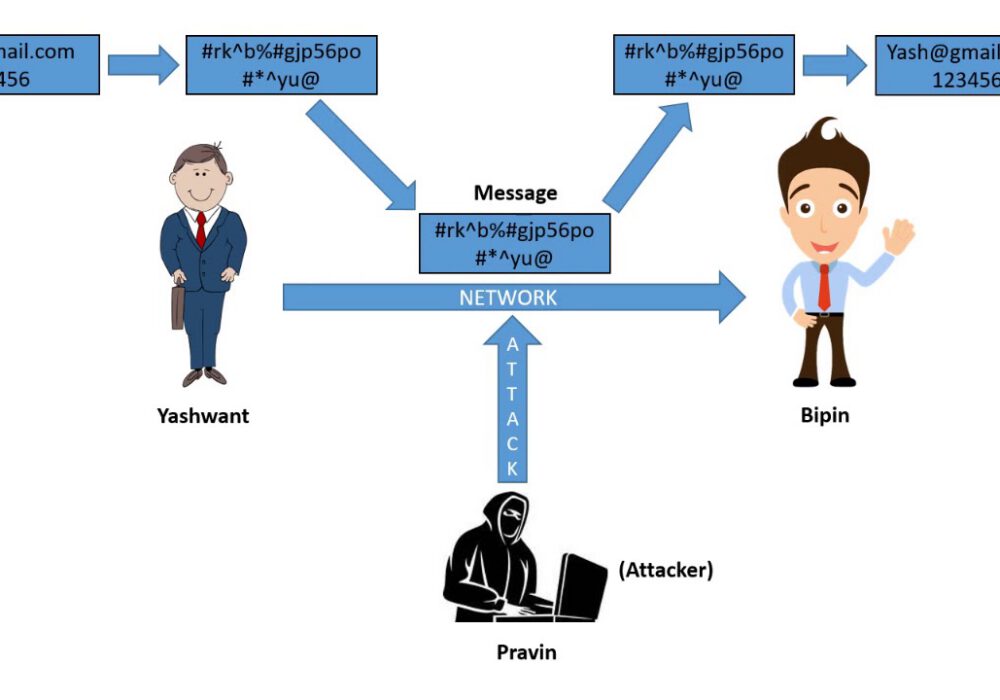
Cryptanalysis is the decryption and analysis of codes, ciphers or encrypted text. Cryptanalysis uses...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
