"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”
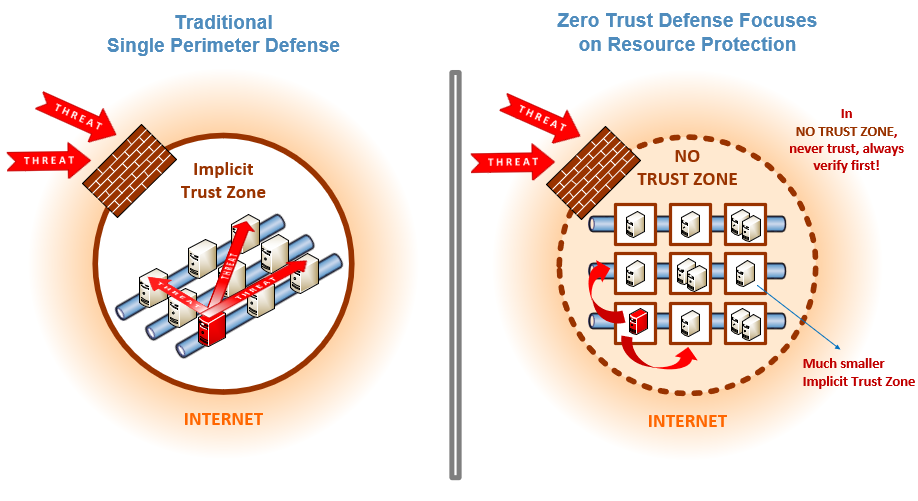
Zero Trust is a security strategy focused on the belief that organizations shouldn't automatically...
Read more
The Ransomware Task Force (RTF) is a group of high-profile security vendors who teamed up with the...
Read more
Bluejacking is the unauthorized sending of messages from one Bluetooth device to another. Bluetooth is...
Read more
Threat Intelligence (TI) is information about current attack tactics and techniques (T&T) used by...
Read more
Threat Hunting is proactive hunting or searching through networks, endpoints, and datasets to find...
Read more
The International Traffic in Arms Regulations (ITAR) is United States regulation that controls the...
Read more
Third-Party Risk Management (TPRM) is the process of identifying, assessing, and controlling risks...
Read more
The Personal Information Protection and Electronic Documents Act (PIPEDA) is Canada's main...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
