“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”

A Service Set Identifier (SSID) is a series of characters that uniquely names a Wireless Local...
Read more
Input Validation, also known as data validation, is the testing of any input (or data) provided by a...
Read more
Business Email Compromise (BEC) is when an email account, often in a company's finance department, is broken into...
Read more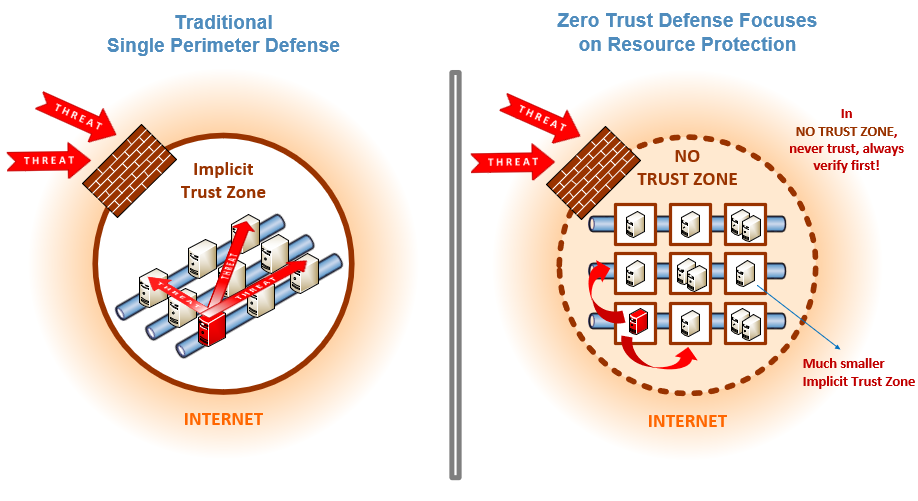
Zero Trust is a security strategy focused on the belief that organizations shouldn't automatically...
Read more
The Ransomware Task Force (RTF) is a group of high-profile security vendors who teamed up with the...
Read more
Bluejacking is the unauthorized sending of messages from one Bluetooth device to another. Bluetooth is...
Read more
Threat Intelligence (TI) is information about current attack tactics and techniques (T&T) used by...
Read more
Threat Hunting is proactive hunting or searching through networks, endpoints, and datasets to find...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
