"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."
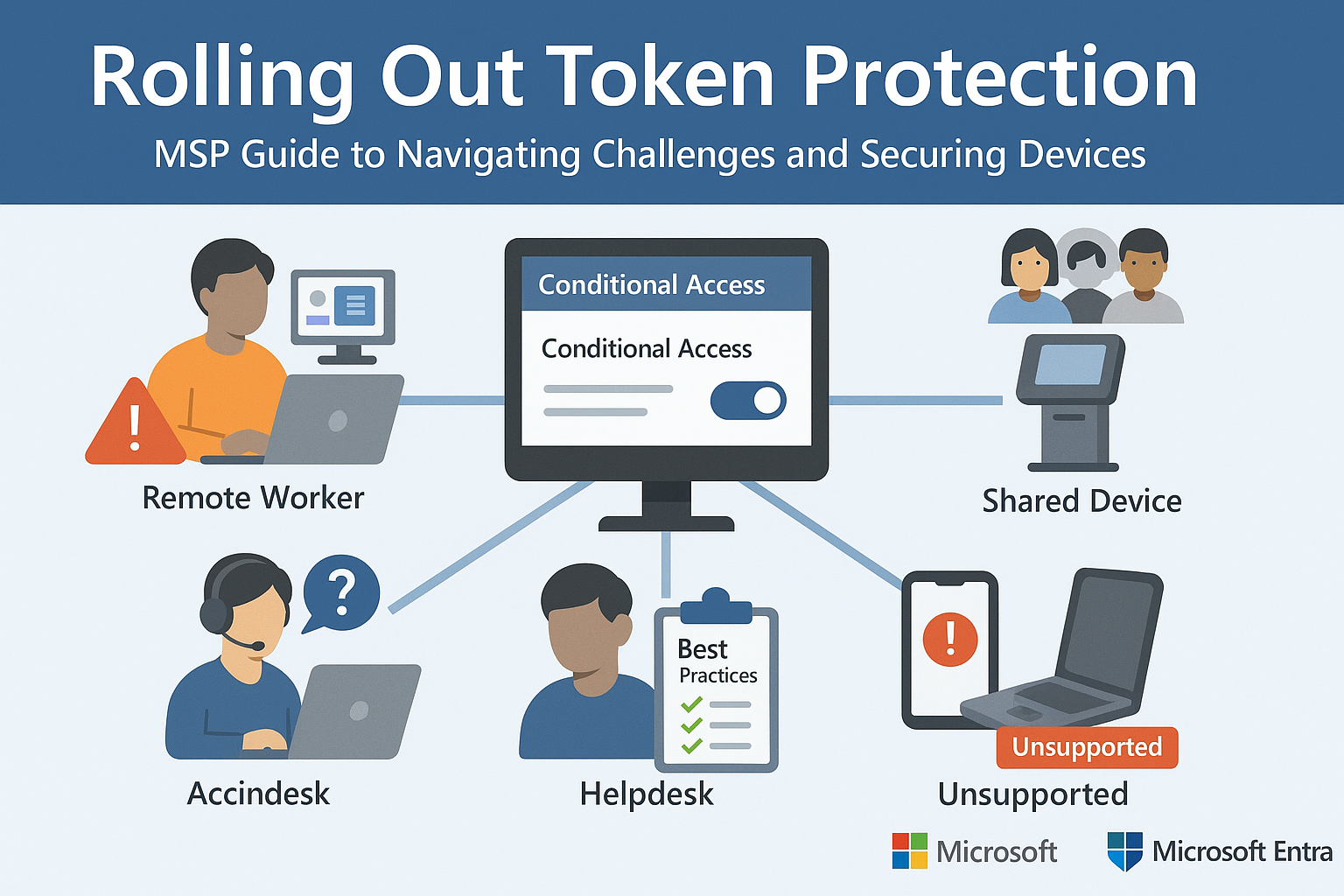
Part 2 of Our Microsoft Entra Security Series In Part 1, we explored how Microsoft’s Token Protection...
Read more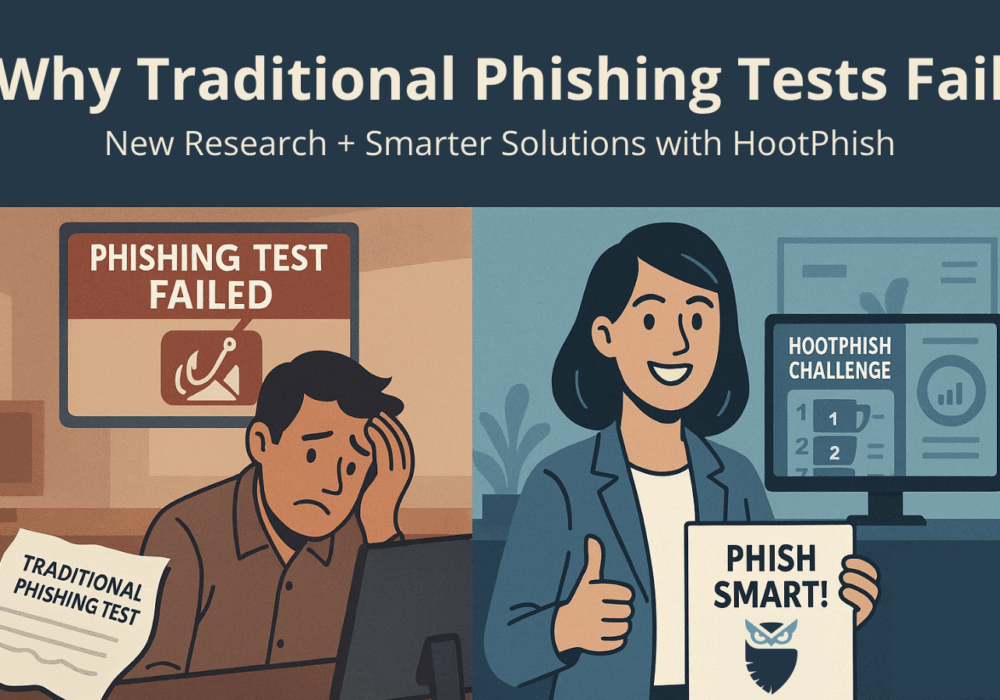
For years, organizations have relied on fake email phishing simulations to measure employee resilience to...
Read more
Welcome to our two-part blog series on Microsoft’s new email security enhancement now included in Office 365 P1...
Read more
"Being an MSP today is like wearing a neon sign that says, ‘Hack me! I’m the gateway to 100...
Read more
Ever had your phone suddenly lose service for no reason, followed by a flood of “reset your password”...
Read more
As smart homes get smarter, so do their habits of watching, sensing, and reporting. Enter WiFi Motion Detection, a...
Read more
Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read more
A recent discovery by cybersecurity firm Oligo Security has unveiled a series of critical vulnerabilities in...
Read more
A newly uncovered cyberattack campaign is exploiting Zoom’s Remote Control feature to infiltrate the systems...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
