
CyberHoot Vulnerability Alert Management Process Rating (VAMP): Critical/Red May 31st, 2022: CyberHoot has learned of a Remote Code Execution (RCE) bug that can be exploited in Microsoft Office files. Security researcher Kevin Beaumont has provided the bug with the name Follina before Microsoft published an advisory about the bug. Microsoft has assigned the identifier CVE-2022-30190 to this bug.
This vulnerability is exploiting users in a variety of ways, but mainly through Phishing emails. The exploit has been reported to work in the following way:
https: URL that gets downloaded.https: URL references an HTML file that contains some odd-looking JavaScript code.ms-msdt: in place of https:.ms-msdt: is a proprietary URL type that launches the MSDT software toolkit.When invoked, the malicious ms-msdt: link triggers the MSDT utility with command line arguments like this: msdt /id pcwdiagnostic ....
If run by hand, with no other parameters, this automatically loads MSDT and invokes the Program Compatibility Troubleshooter, which looks innocent enough, like this:
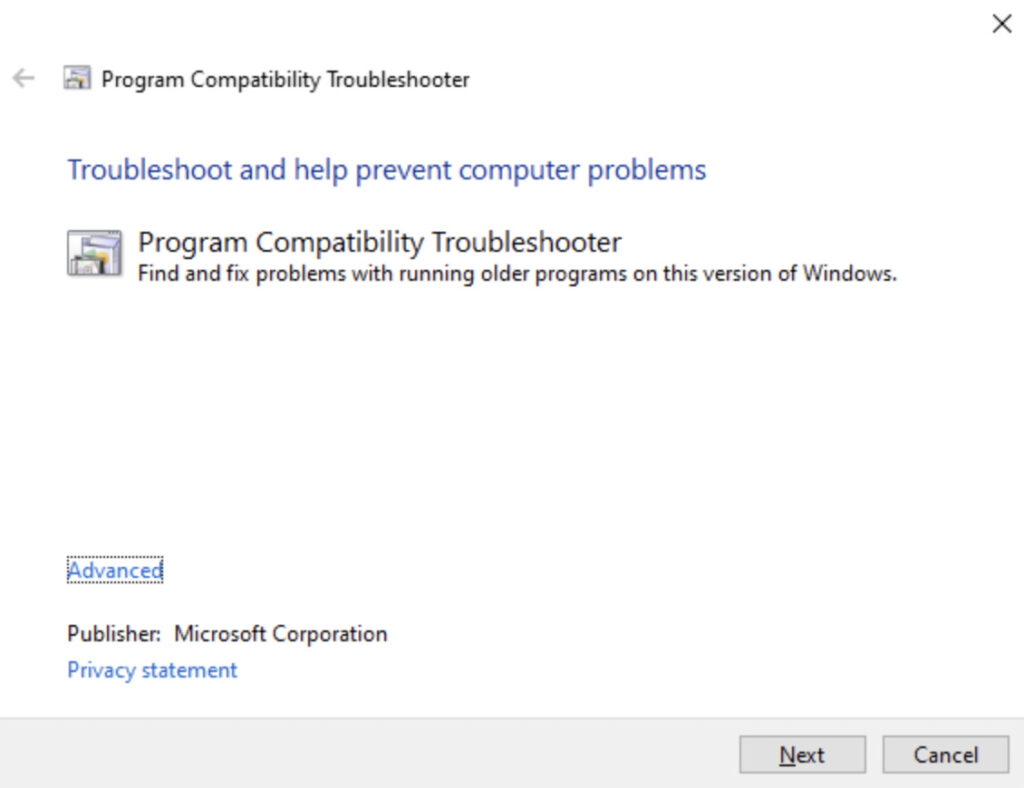
From here, you can choose an app to troubleshoot, answer a bunch of support-related questions, perform various automated tests on the app, and if you’re still stuck, you can choose to report the problem to Microsoft, uploading troubleshooting data at the same time.
You probably wouldn’t expect to get thrown into this PCWDiagnostic utility just by opening a document, you’d at least see a series of popup dialogs and you’d get to choose what to do at every step of the way.
Unfortunately, instead of getting asked how you want to proceed, the crooks have crafted a sequence of parameters that not only cause the malicious operation to proceed automatically (e.g. the options /skip and /force), but also to invoke a PowerShell script along the way.
Worse still, this PowerShell script doesn’t have to be in a file on disk already, it can be provided in scrambled source code form right on the command line itself, along with all the other options used. The PowerShell is used to extract and launch executable malware provided in compressed form by the hackers.
As convenient as Microsoft’s proprietary ms-xxxx URLs may be, the fact that they’re designed to launch processes automatically when specific types of files are opened, or even just previewed, is certainly a security risk.
A workaround that was quickly agreed upon in the community, and has been officially endorsed by Microsoft, is simply to break the relationship between ms-msdt: URLs and the MSDT utility. This means that ms-msdt: URLs no longer have any special significance, and can’t be used to force MSDT.EXE to run.
You can make this change simply by removing the registry entry HKEY_CLASSES_ROOTms-msdt if it exists. If it’s not there, then you are already protected.
If you create a file with a name ending .REG that contains this text…
Windows Registry Editor Version 5.00 [-HKEY_CLASSES_ROOTms-msdt]
…you can double-click the .REG file to remove (the minus sign means “delete”) the offending entry.
You can also browse to HKEY_CLASSES_ROOTms-msdt in the REGEDIT utility and hit [Delete].
Or you can run the command: REG DELETE HKCRms-msdt.
Note that you need administrator privileges to modify the registry in this way.
If you discover that you just can’t live without ms-msdt URLs, you can always replace the missing registry data later.
To back up the HKEY_CLASSES_ROOTms-msdt registry key, use the command: REG EXPORT HKEY_CLASSES_ROOTms-msdt backup-msdt.reg.
To restore the deleted registry key later, use: REG IMPORT backup-msdt.reg.
If you’re a subscriber to CyberHoot’s services, you’ll have access to our Policy and Process library which contains the vulnerability alert management process document. This document prescribes how to respond to situations like this and in what time frame. If your company has not yet adopted a VAMP-like process, now is a great time to get started.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
