"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”

Image Source Supply Chain Risk Management refers to the process of identifying, analyzing, and assessing...
Read more
Risk Reduction (limitation) is the most common risk management strategy used by businesses. This...
Read more
Image Source Risk Acceptance (Accept) refers to accepting the risk that is presented to you or your...
Read more
Image Source Avoidance refers to avoiding the risk that is found altogether. When mitigating risk, there are...
Read more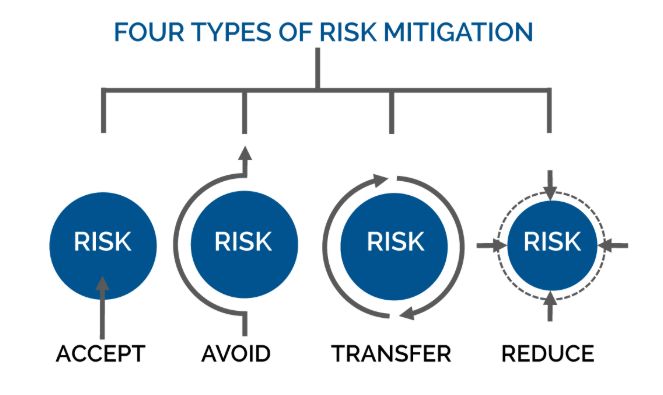
Image Source Mitigation occurs when assessing risk. When assessing risk there are many ways to work...
Read more
Image Source An investigation is a systematic and formal inquiry into a qualified threat or...
Read more
Image Source A malicious applet is a small application program that is automatically downloaded and...
Read more
Image Source Malicious Logic is hardware, firmware, or software that is intentionally included or...
Read more
Symmetric Cryptography is a branch of cryptography in which a cryptographic system or algorithms use...
Read more
A Symmetric Key is a cryptographic key that is used to perform both the cryptographic operation and...
Read more
Image Source System Integrity is the attribute of an information system when it performs its...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
