"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."

Image Source Information Sharing is an exchange of data, information, and/or knowledge to manage risks or...
Read more
Information System Resilience is the ability of an information system to: (1) continue to operate under...
Read more
Image Source Information Systems Security Operations in cybersecurity work is where a person: Oversees...
Read more
Image Source Interoperability is the ability of two or more systems or components to exchange information...
Read more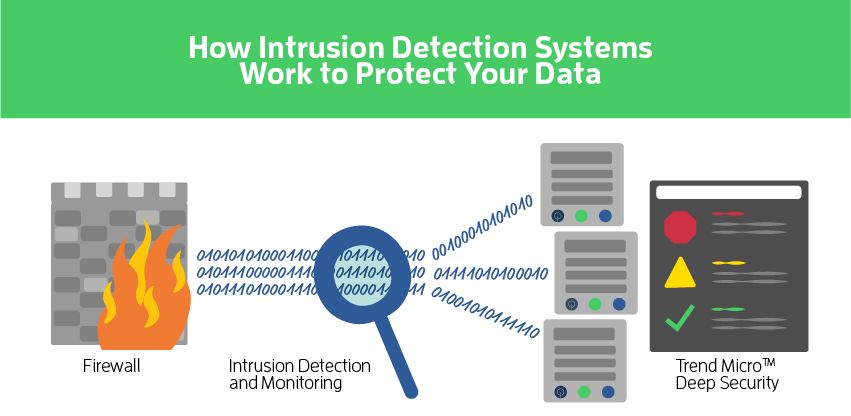
Network-based Intrusion Prevention Services (aka NIPS) is a preemptive approach to network security used to...
Read more
Image Source Intrusion Detection is the process and methods for analyzing information from...
Read more
Image Source Information Technology (IT) is any equipment or interconnected system or subsystem of equipment...
Read more
Image Source Information and Communication(s) Technology (ICT) is any information technology,...
Read more
Image Source Machine Learning and Evolution is a field concerned with designing and developing artificial...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
