"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."
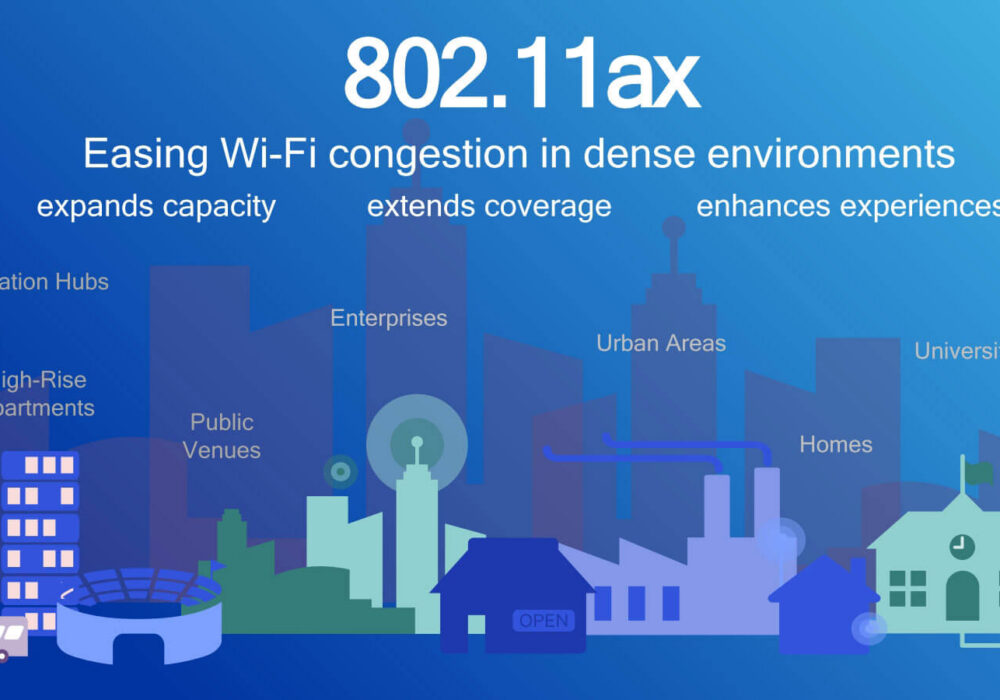
Do you ever get frustrated with your Internet speeds and find yourself saying "there's no way this is...
Read more
Cyber Insurance is a form of insurance for businesses and individuals against Internet-based threats....
Read more
Experts are warning security professionals of the next big threat hitting the cyber world: Application...
Read more
Digital Content Management (DCM) is the process for collection, delivery, retrieval, governance...
Read more
Cyberwarfare is the use of sophisticated cyber weapons (viruses, worms, trojans, etc.) by one...
Read more
An Application Programming Interface (API) is a set of definitions and protocols for building...
Read more
The Tor Browser is a web browser designed for anonymous web browsing and protection against traffic...
Read more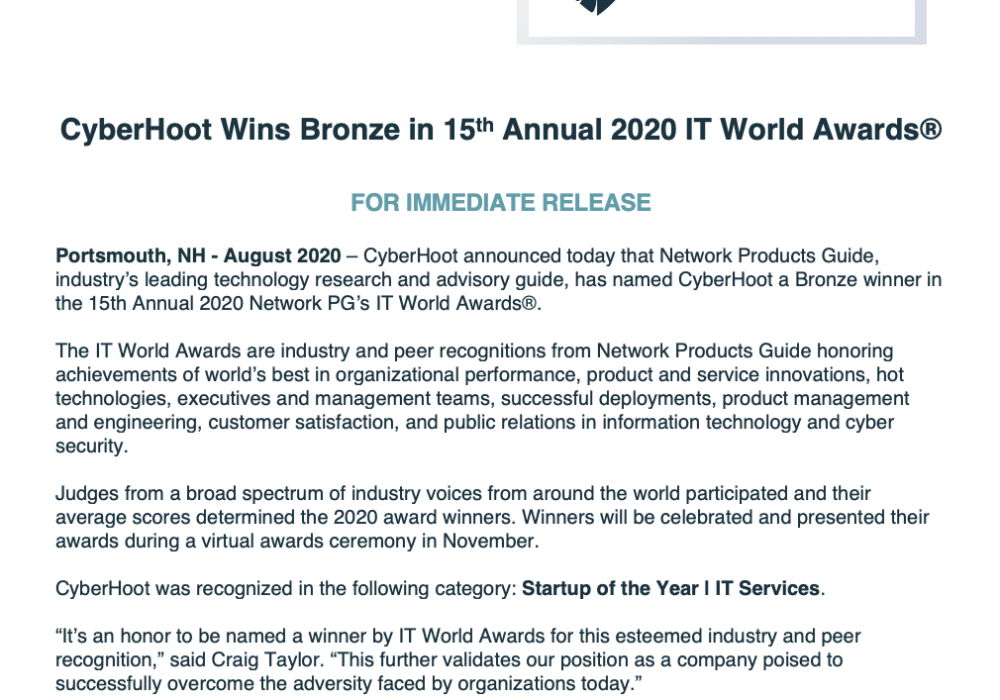
Click To View Larger Version CyberHoot’s Press Releases are published on a monthly basis. To see the...
Read more
If you would like to find more of our infographics, you can head here. You can also check out our 31 Days of...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
