Recently, cryptocurrency exchanges, the place where you can buy and sell cryptocurrencies on the Internet, have been under active and successful attack. In one case, a Chinese cryptocurrency exchange called Poly Networks was robbed of about $600 million’s worth of cryptocurrencies. Luckily the hacker was ethical enough to give a most, if not all (eventually) back to Poly Networks after they promised to fix the flaw he exploited. A few weeks after the Poly Networks incident, a Japanese-based cryptocurrency platform, Liquid, got hit by hackers, who stole $100 million worth of their cryptocurrency. What’s going on?
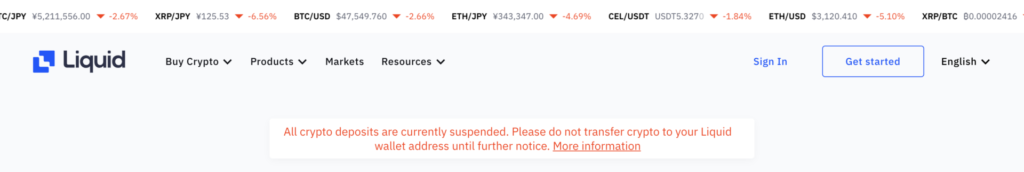
Details are not public yet on how the $100 million dollars in cryptocurrency was stolen. What we do know, is Liquid decided to suspend all crypto deposits and withdrawals from user’s wallets until further notice (see screenshot below).
If you click on the ‘More information‘ link, it allows you to subscribe to future updates on the status of the crypto trading platform. The page mentions they’re moving all of their assets to a Cold Wallet until the situation is settled. A Cold Wallet is a form of Cryptocurrency Wallet, also known as Hardware Wallets, where keys are stored in a thumb-drive device that is kept in a safe place (away from hackers) and only connected to a computer when users want to use their crypto. The currency contained in a cold wallet is further protected with strong encryption making it very secure even if the device is stolen, although the owner no longer has access to the coins either. This is the most secure way to protect private keys from theft.
Cryptocurrency companies can pop up out of nowhere. You cannot assume that your Cryptocoins are properly protected in the same way as you assume your bank deposits are protected. There is no FDIC protection on Cryptocurrencies. Hosting a cryptocurrency exchange securely requires an enormous amount of high technology and sophisticated cybersecurity. Banks can do these things, but these thefts reveal how weak the overall cybersecurity of cryptocurrency exchanges truly is. CyberHoot would not trust more than $1000 in any one cryptocurrency exchange as it appears to us to be too risky.
If you’re a Liquid user, there isn’t much you can do right now until they figure out the situation themselves. Maybe the same hacker who broke into Poly Networks broke into Liquid and the currencies will be returned, but it is very highly unlikely. CyberHoot does, however, recommend the following measures to reduce your likelihood of becoming a victim of cryptocurrency theft. Follow these measures to reduce your risk.
There are more than 10,000 different cryptocoins currently in trading, many of which were kicked off by cash injections from early investors. It’s important to understand not all cryptocurrencies will follow the Bitcoin pattern (or even standard stock trading patterns) of going from a few cents in value in 2010 to $45,000 in August 2021. Also, some emerging cryptocurrencies have been outright scams where the creators of the coin collect startup funds from early investors in what’s known as an ICO (initial coin offering), only to run off without ever establishing the new cryptocurrency at all. So you might want to start off small with micro investing and play it safe
A cold wallet seems to be the most secure way to store cryptocurrencies outside of the currency exchanges. You can control the physical world more easily than the virtual world to protect your investment. Just don’t be that guy, who’s seeking to dig up an old hard drive with 280 million dollars worth of bitcoins because he accidentally threw away 7500 bitcoin in a local dump.
In addition to keeping those recommendations in mind, CyberHoot recommends the following best practices to protect individuals and businesses against, and limit damages from, online cyber attacks:
Sources:
Additional Readings:
Crypto Platform Poly Network Says Hacked Funds Returned
Hackers Hit Japanese Crypto Exchange, Steal Nearly $100 million
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Ever had your phone suddenly lose service for no reason, followed by a flood of “reset your password”...
Read more
As smart homes get smarter, so do their habits of watching, sensing, and reporting. Enter WiFi Motion Detection, a...
Read more
Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
