January 14th, 2020: Today Microsoft released their monthly patches and amongst them were three critical Severity 1 issues that need your immediate attention. Businesses should invoke the Vulnerability Alert Management Process to triage these alerts, and immediately plan patching as soon as possible. Please consider this special blog advisory from CyberHoot as a very unusual circumstance and take appropriate action as soon as possible. To put this in perspective – ALL my cybersecurity sources are suggesting the same thing. Government cybersecurity watchdog entities such as CISA issued only its second Emergency Directive ever for these vulnerabilities. This is serious.
CryptoAPI spoofing vulnerability – CVE-2020-0601: This vulnerability affects all machines running 32- or 64-bit Windows 10 operating systems, including Windows Server versions 2016 and 2019.
Windows RD Gateway and Windows Remote Desktop Client vulnerabilities – CVE-2020-0609, CVE-2020-0610, and CVE-2020-0611: These vulnerabilities affect Windows Server 2012 and newer. In addition, CVE-2020-0611 affects Windows 7 and newer.
This section of the advisory outlines the potential impact if these vulnerabilities were exploited.
CryptoAPI spoofing vulnerability – CVE-2020-0601:
Windows RD Gateway and Windows Remote Desktop Client vulnerabilities – CVE-2020-0609, CVE-2020-0610, and CVE-2020-0611:
As a matter of fact yes. [whew!] These vulnerabilities were discovered and reported, for the first time, by the NSA, to Microsoft directly. This means we have a very small window upon which to apply these patches without a large risk of compromise.
However, a very small window of Internet time could mean days or weeks.
By analyzing the patches Microsoft released today, bad actors can quickly identify what code was changed. The patches are like a treasure map for hackers to follow, via source code changes, reverse engineering them, until they find the vulnerability. Then they weaponize it them. There is a race going on as we speak to identify and weaponize these vulnerabilities by nation states and hacker groups. We have days, maybe weeks, before these vulnerabilities are weaponized and begin to exploit your systems.
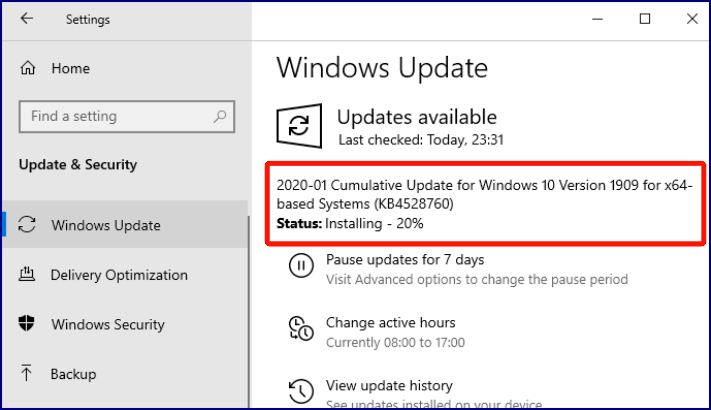
Your Windows version number may vary, but this is the update you want – go to Settings > Update & Security > Windows Update:
https://cyber.dhs.gov/ed/20-02/
https://www.us-cert.gov/ncas/alerts/aa20-014a
Brian Krebs Cybersecurity News Blog
Sophos Cybersecurity Blog – Microsoft Critical Vulnerabilities = Patch Now
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
