
March 1st, 2023: Multiple vulnerabilities found in ConnectWise Recover and R1Software leveraging ZK Framework for Java web development. These vulnerabilities allow for arbitrary code execution, privilege escalation, and may enable hackers to deploy ransomware/backdoors via remote backup services. Recommendation: Patch impacted systems immediately and investigate to ensure hackers have not already compromised networks.
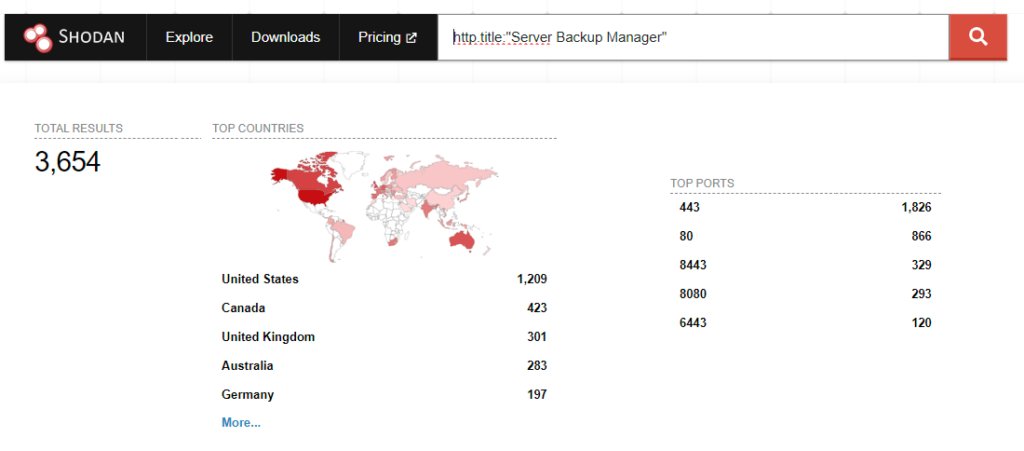
CyberHoot heard from Rapid7 today of active exploitation of CVE-2022-36537 in vulnerable versions of ConnectWise R1Soft Server Backup Manager software. The underlying vulnerability is tied to the ZK Framework. This is an open-source Java framework used for creating web applications. ConnectWise uses ZK Framework in its popular R1Soft and Recovery products. The vulnerability is being used for remote code execution and installation of malicious drivers that may include remote access functionality. Upon successful compromise, attackers have been able to execute commands on all systems running ConnectWise’s backup agent connected to the R1Soft server.
This ConnectWise advisory and NVD entry for CVE-2022-36537 report the flaw as an information disclosure vulnerability. Rapid7 believes this categorization significantly downplays the risk and the impact of CVE-2022-36537. CyberHoot and Rapid7 believe this under-reports the criticality of this risk. Instead we recommend emergency assessment and patching of your impacted systems.
Additionally, there are other ZK Framework integrations that will likely come to light in the coming days or weeks. Please check your environment(s) for any other solutions using the exposed Java ZK framework.
ConnectWise Recover: Recover v2.9.7 and earlier versions are impacted.
R1Soft: SBM v6.16.3 and earlier versions are impacted.
What Should You Do?
Companies should check their inventory of hardware and software assets looking for ZK Framework use. Patch immediately if you are at risk.
Review vulnerability scan data for additional exposure. In all cases, follow your Vulnerability Alert Management Process (VAMP) and patch according to the timelines required.
For CyberHoot vCISO clients, this is a critical severity issue that should be patched immediately when and where found due to the significant potential for highly impactful compromises of multiple devices and systems.
According to the ConnectWise advisory, affected ConnectWise Recover SBMs have automatically been updated to the latest version of Recover (v2.9.9). However, for R1Soft, upgrade the server backup manager to SBM v6.16.4 released October 28, 2022 using the R1Soft upgrade wiki from ConnectWise.
ZK Framework is an open source Java framework used to create web applications. Since we know ConnectWise uses this framework, we know there are patches to apply. There may be many other Web Applications out there using this Java Framework. Please assess your web application exposure independent of advisories from CyberHoot, ConnectWise or others to determine other points of risk to your organization.
Rapid7 Blog Advisory on In the Wild Exploits of ConnectWise Recover and R1Soft Server Backup SolutionsCybersecurity and Infrastructure Security Administration AdvisoryConnectWise Security BulletinNational Vulnerability Database Entry – CVE 2022 – 36537
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
