"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
Symmetric Cryptography is a branch of cryptography in which a cryptographic system or algorithms use...
Read more
A Symmetric Key is a cryptographic key that is used to perform both the cryptographic operation and...
Read more
Image Source System Integrity is the attribute of an information system when it performs its...
Read more
Image Source Tailored Trustworthy Space refers to a cyberspace environment that provides a user with...
Read more
Image Source A Threat Agent is an individual, group, organization, or government that conducts or...
Read more
Image Source Threat Analysis in cybersecurity work is where a person identifies and assesses the...
Read more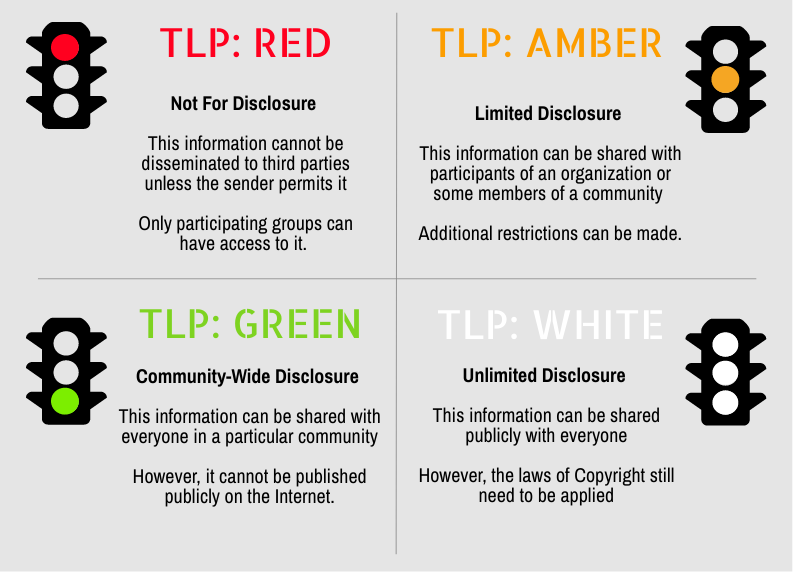
Secure your business with CyberHoot Today!!! Sign Up Now Traffic Light Protocol (TLP) is a set of...
Read more
A Trojan Horse is a computer program that appears to have a useful function, but also has a hidden and...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
