
Intersection of Threats, Assets, and Vulnerabilities is your Risk
Risk is the potential for an unwanted or adverse outcome resulting from an incident, event, or occurrence, as determined by the likelihood that a particular threat will exploit a particular vulnerability, with the associated consequences.
Risk is the combination of threats and vulnerabilities to an asset. Risk is calculated in business by looking at three different categories.
The Annual Loss Expectancy is calculated by using this formula: ARO x SLE = ALE.
Source: DHS Risk Lexicon, NIPP and adapted from: CNSSI 4009, FIPS 200, NIST SP 800-53 Rev 4, SAFE-BioPharma Certificate Policy 2.5
Related Terms: Threat, Vulnerability
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
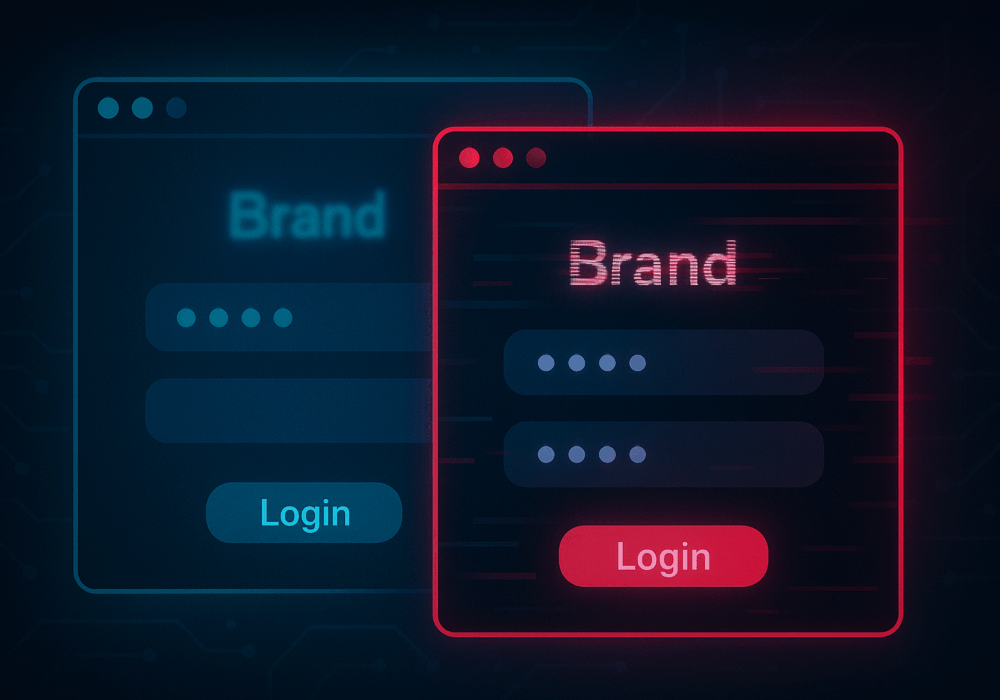
In cybersecurity, not all attacks happen through fancy malware or zero-day exploits. Some of the most effective...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
