"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
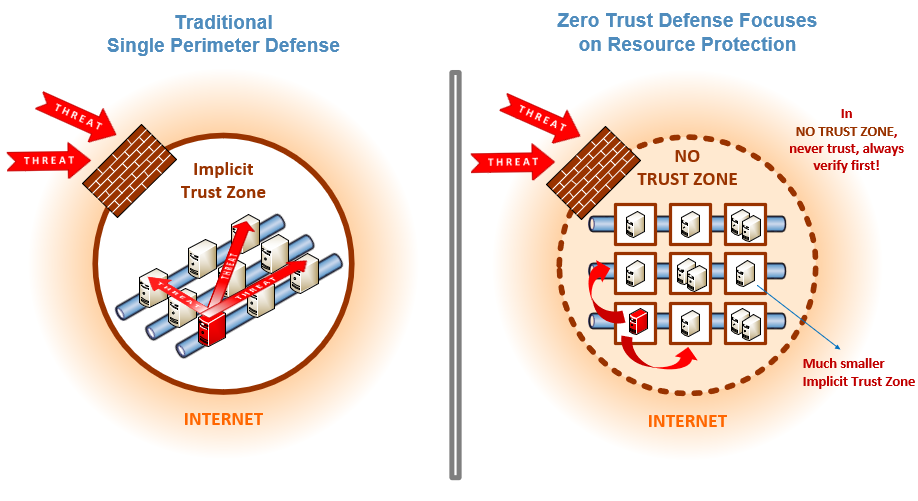
Zero Trust is a security strategy focused on the belief that organizations shouldn't automatically...
Read more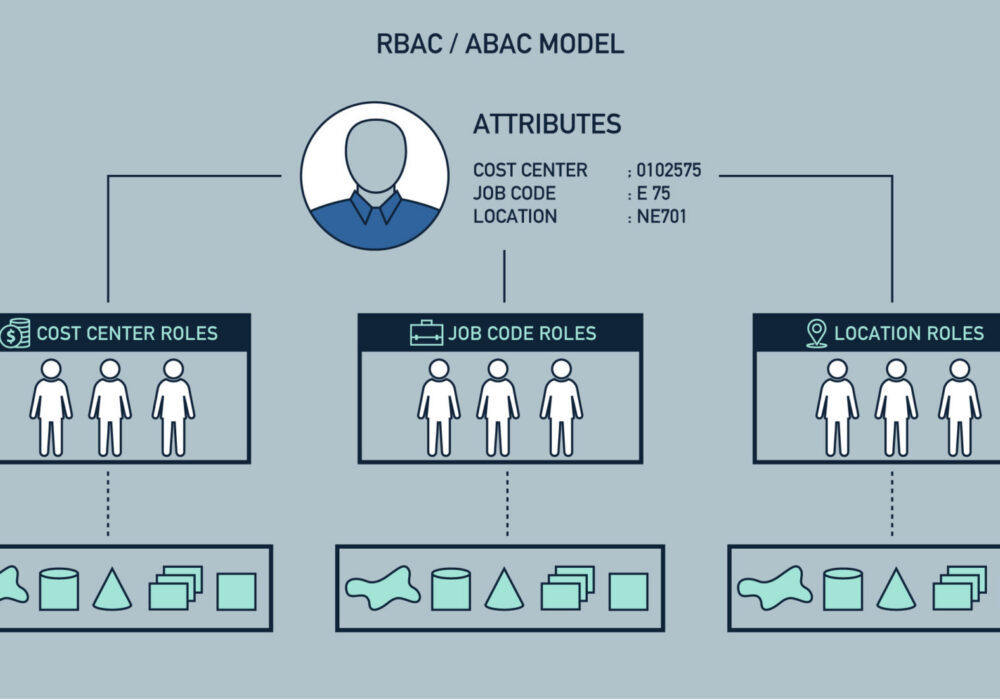
Role-Based Access Control (RBAC) is a strategy of limiting network access based on the roles of...
Read more
A Privileged User is a user of a computer who is authorized to bypass normal access control mechanisms,...
Read more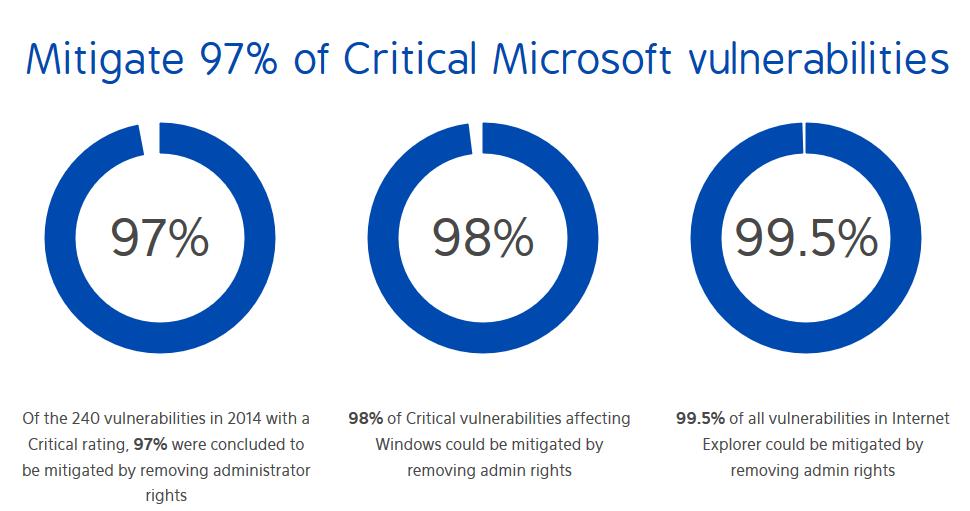
Administrator Rights is the highest level of permission given to a computer user. A user with...
Read more
Least Privilege refers to the access that is given to a user on a device or computer. Giving a...
Read more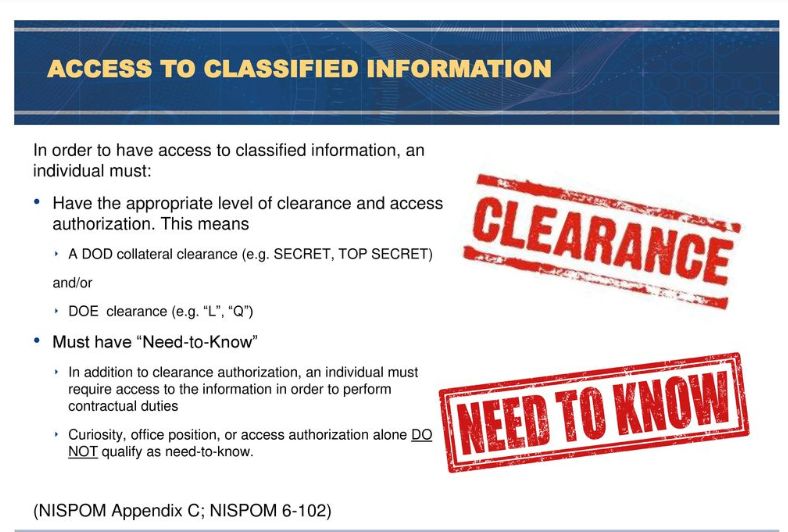
Need to Know is a term that applies to sensitive and often classified information. It is a...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
