"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."

Nation State hackers are the best of the best. Their attacks are evolving and are not often seen...
Read more
Image Source Cloud Computing is a model for enabling on-demand network access to a shared pool of...
Read more
Computer Network Defense is the actions taken to defend against unauthorized activity within computer...
Read more
Authentication is the process of verifying the identity or other attributes of an...
Read more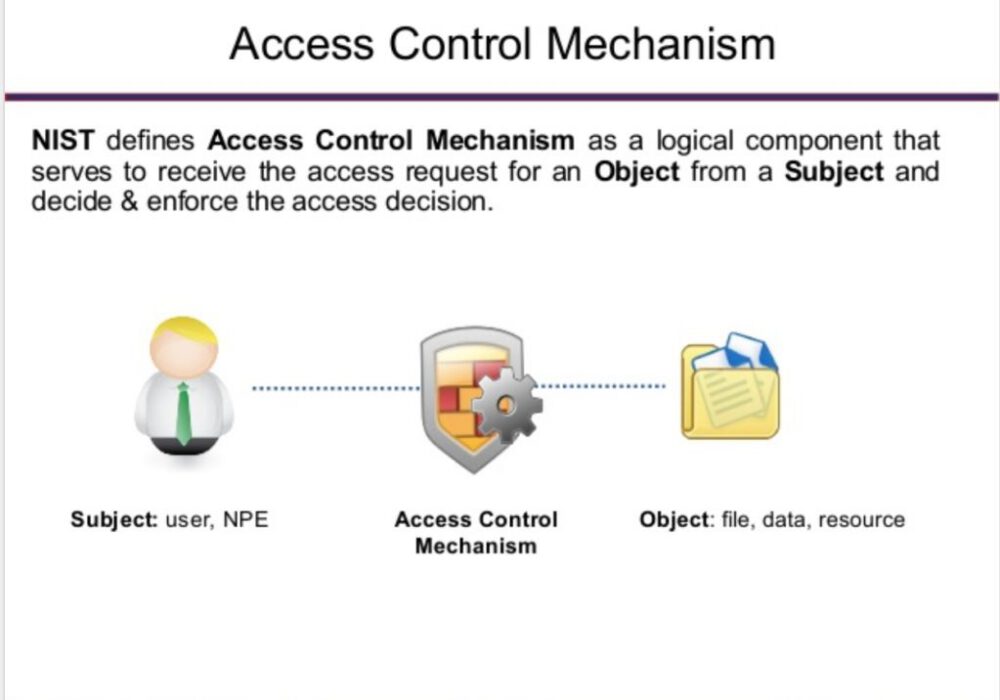
Image Source An access control mechanism is a security safeguard (i.e., hardware and software...
Read more
A Block List or Deny List, (deprecated: Blacklist), is a list of entities that are blocked or...
Read more
Image Source Active content is software that is able to automatically carry out or trigger actions without...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
