"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.
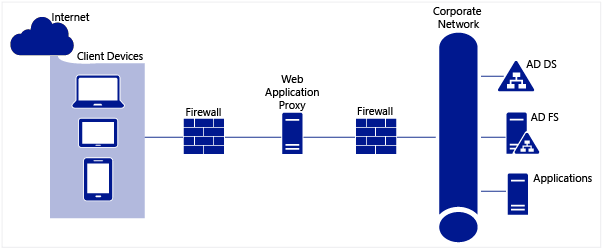
An Application Proxy is one of the most secure firewall types that can be deployed. The...
Read more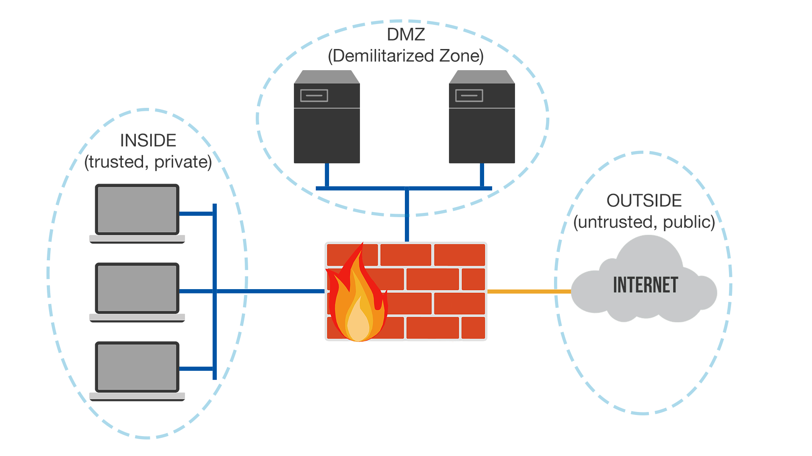
The Demilitarized Zone (DMZ) is sometimes referred to as a "perimeter network", its primary...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
