Welcome back to Episode 3 of Shoot the Hoot—the weekly livestream hosted by Chuck Taylor, Co-Founder and Lead Developer at CyberHoot. If you’re an MSP or SMB who’s tired of cybersecurity snoozefests and ready for some straight-up real talk, you’re in the right place.
This week, we’re going full origin story. Chuck takes us all the way back to where CyberHoot began—how it started, what’s broken (and fixed) along the way, and why we still believe in breaking things…lovingly. From garage-level chaos to Autopilot awesomeness, this episode’s got the behind-the-scenes, the hard-earned lessons, and a few too many dad jokes.
Still raw. Still ridiculous. Still 100% for the MSP community.
🛫 Today’s Flight Plan:
🦉 Back to the Beginning – The true story of how CyberHoot was born (spoiler: it wasn’t pretty)
🦉 Autopilot Showcase – What it is, what it does, and why it’s changing the game
🦉 Lessons from the Trenches – The wins, the losses, and the “what were we thinking?” moments
🦉 Ask Chuck Anything – Unfiltered Q&A with zero buzzwords
Whether you’re building your own thing or just want to know how the heck we got here, this episode proves (again) that cybersecurity can be useful and hilarious.
No fluff. No filters. Just real stories from the frontline.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

If a Chrome extension promises to remove security pop-ups and generate MFA codes, that should make you...
Read more
Cyberattacks usually start with phishing emails or weak passwords. This one did not. Security researchers...
Read more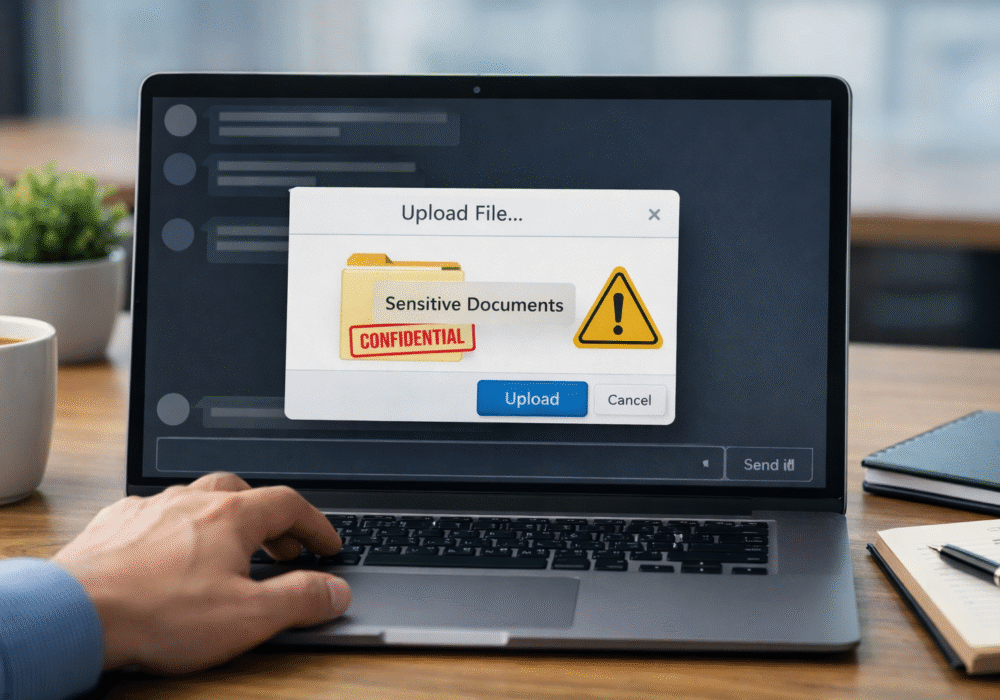
Not surprising when Trouble Ensues Last summer, the interim head of a major U.S. cybersecurity agency uploaded...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
