CyberHoot gives you the flexibility to assign policies, videos, and programs to your users as optional learning resources. These assignments are ideal for offering valuable training without triggering repeated reminders or enforcing strict compliance requirements.
Optional assignments are tracked separately from compliance data, ensuring your compliance metrics remain accurate and unaffected. This allows you to provide supplemental content without skewing your reports.
Here’s how to get started…
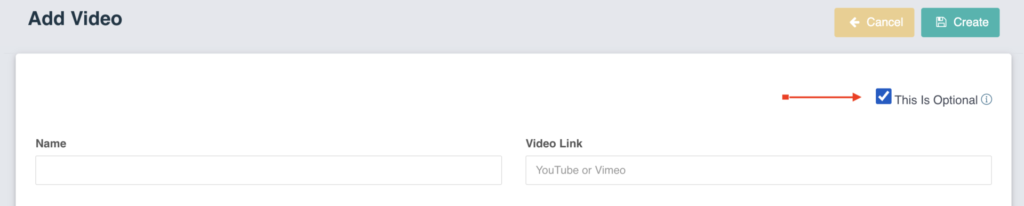
When creating or cloning a policy, simply check the ‘This is Optional’ checkbox in the upper right hand corner of the card as seen here:

When creating or cloning a policy, simply check the ‘This is Optional‘ checkbox in the upper right hand corner of the card as seen here:
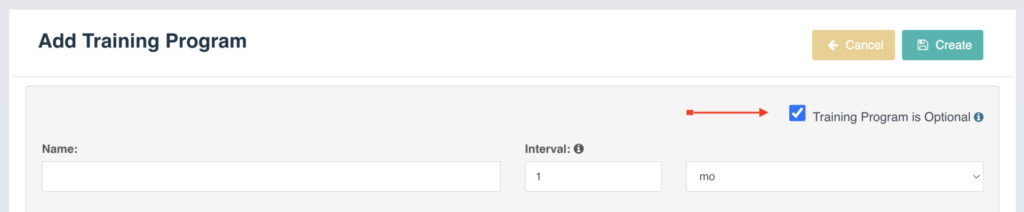
Once a program is added, you can assign the training program to a group of users as an optional training program by checking the ‘Training Program is Optional‘ checkbox in the upper right hand corner of the card as seen here:
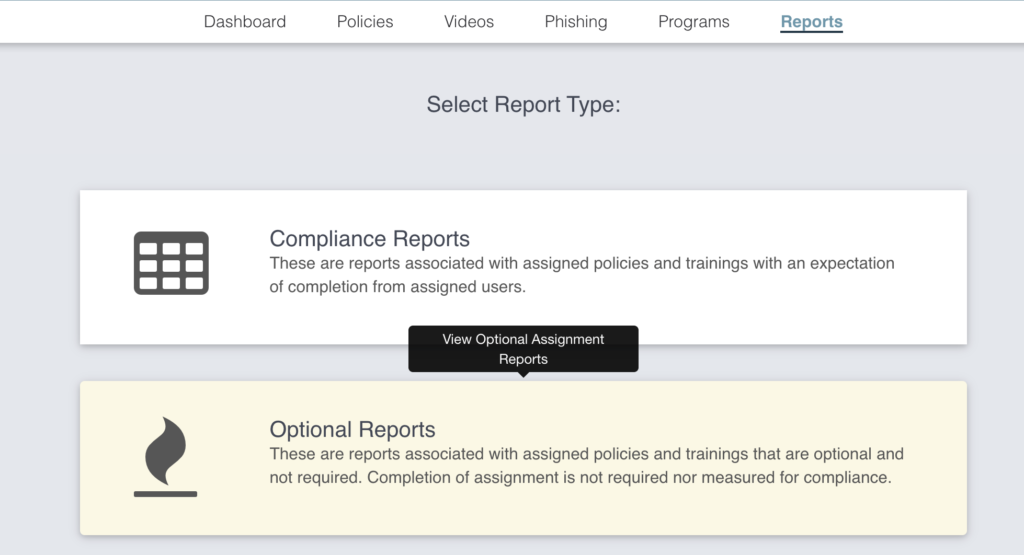
You can view the Optional Reports by click on the Reports link in the navigation bar and clicking the Optional Reports card, which will take you to the Optional Reports page.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Ransomware groups are not breaking in organizations the same way they did five years ago. The entry methods have...
Read more
If a Chrome extension promises to remove security pop-ups and generate MFA codes, that should make you...
Read more
Cyberattacks usually start with phishing emails or weak passwords. This one did not. Security researchers...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
