"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."
This 3-minute video outlines how to create strong passphrases by using at least five (5) discrete words that are...
Read more
This short 3 min video outlines how to combat malware by preventing it from being installed in the first...
Read more
This 20 minute Ted Talk discusses how a hidden cyberwar is being perpetrated for the past 2 decades online not...
Read more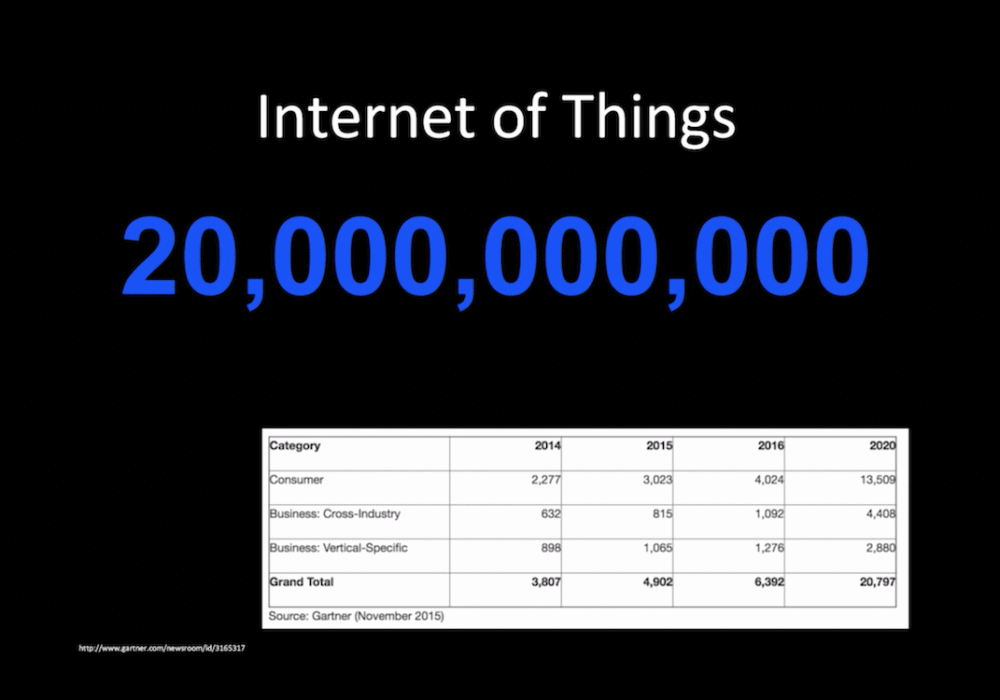
This 12 minute Ted Talk outlines how the IoT is making investigations easier. Digital forensics looks for a...
Read more
This 16 minute Ted talk outlines the work of a digital forensics investigator. He describes his work...
Read more
This video outlines the steps you need to take to setup your DMARC and DKIM email records in the Domain Name...
Read more
https://www.youtube.com/embed/5XbSNeVsQYcThis video covers the most common types of insiders who threaten your...
Read more
https://www.youtube.com/embed/xLyPhLHlyXE This Fox News special outlines an alert posted by Twitter about hacker...
Read more
Computer security in the 21st century isn’t solely about password hygiene and phishing attacks. It must also...
Read more
https://www.youtube.com/embed/qbuSZ9rOKNk Hospitals must train all their employees on how to remain safe while...
Read more
https://www.youtube.com/embed/sxybmE1rrZg The FBI claims that over 50% of the 6 Trillion dollars lost to hackers...
Read more
The Healthcare market is required to provide training on legislation that was passed over a decade ago and called...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
