"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”
This 20 minute Ted Talk discusses how a hidden cyberwar is being perpetrated for the past 2 decades online not...
Read more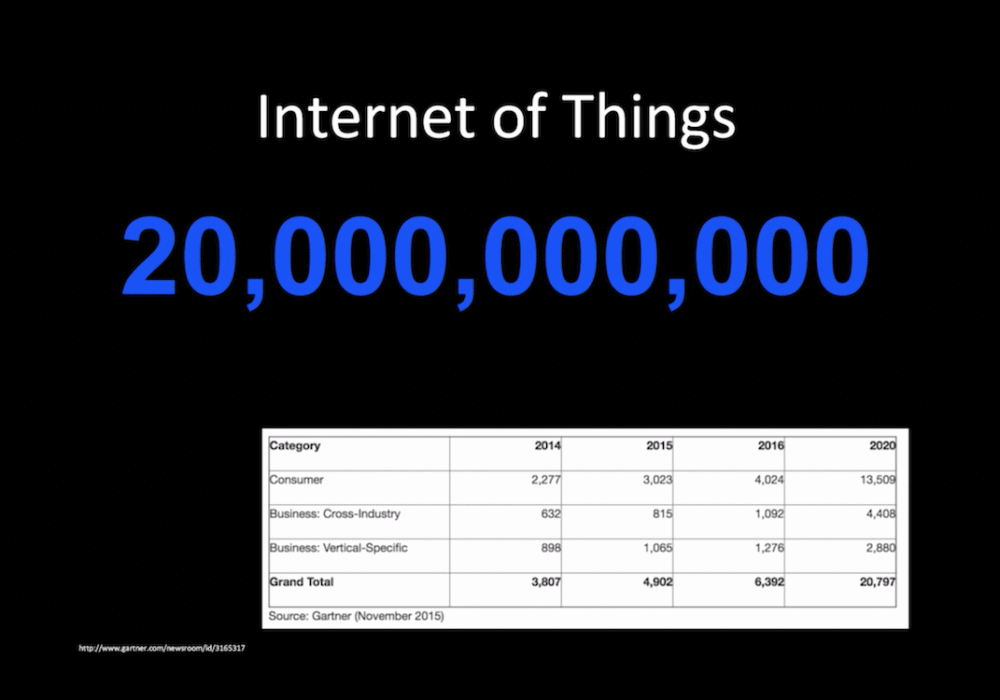
This 12 minute Ted Talk outlines how the IoT is making investigations easier. Digital forensics looks for a...
Read more
This 16 minute Ted talk outlines the work of a digital forensics investigator. He describes his work...
Read more
This video outlines the steps you need to take to setup your DMARC and DKIM email records in the Domain Name...
Read more
This 5 minute video outlines how Password Managers can make your life easier. It starts by illustrating some of...
Read more
What happens when you sit down at your computer in the morning after a long vacation or jury duty or...
Read more
What happens when you sit down at your computer in the morning after a long vacation or jury duty or...
Read more
LastPass lives in your browser as an extension. It sits in the background monitoring your logins to each website...
Read more
The LastPass password manager is a security and productivity tool for the 21st century. Watching this video...
Read more
The first thing you need to learn with LastPass, or any password manager, is how it saves your online identities...
Read more
One of the more difficult tasks associated with strong password hygiene is creating strong passwords. This 1...
Read more
This 1 minute video outlines how to create secure encrypted note cards within LastPass. These notecards are...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
