A Practical Brief for vCISOs
For years, the most credible voices in AI research have issued the same warning. Treat artificial intelligence with the same institutional seriousness the world applied to nuclear technology. Warren Buffet put it plainly at the 2024 Berkshire Hathaway shareholder meeting:
“We let a genie out of the bottle when we developed nuclear weapons. AI is somewhat similar — it’s part way out of the bottle.” Source: CNN Business, May 2024
If you’re like me, given the gravitas of the people warning us (Stephen Hawking, Geoffrey Hinton, Bill Gates), we tried understanding these warnings. Unfortunately, for most of us, the warnings felt abstract and impossible to conceptualize. The potential disruptions seemed distant, murky, closer to science fiction than reality. The genie was still in the bottle and Pandora’s Box was still firmly closed.
On April 7th , 2026, Anthropic briefly cracked the lid with an AI model called Claude Mythos preview. What they found inside concerned them enough to close it for the general public and restrict access to a curated coalition of critical software infrastructure providers. The hope was to get ahead of what this model represents before adversaries do the same.
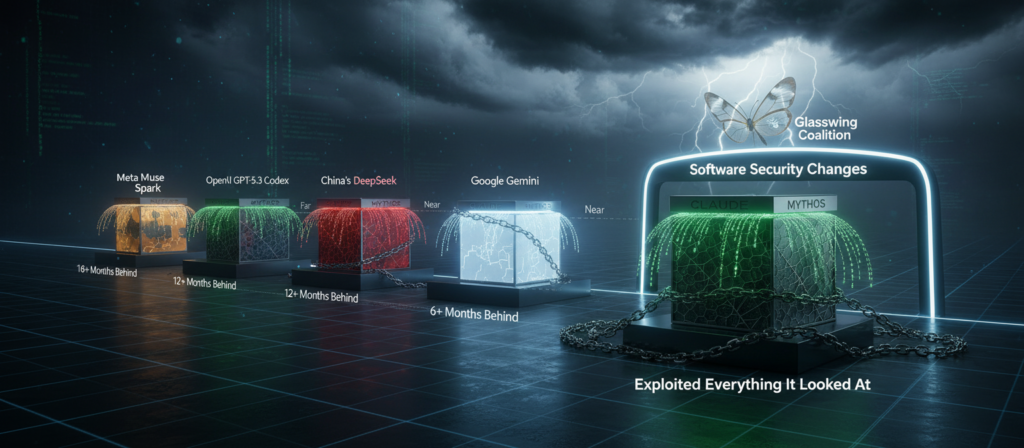
Anthropic revealed that Claude Mythos located critical software vulnerabilities, known as zero-days, in every major operating system and browser they pointed it at. So Anthropic closed the box and refused to release it publicly. Instead, they assembled a coalition called Project Glasswing, drawing in roughly 40 to 50 of the world’s largest software infrastructure providers, including Microsoft, Google, Apple, Amazon, Cisco, and CrowdStrike. The goal was to use Mythos to find and patch vulnerabilities before adversaries could weaponize them.
The results were significant. Mythos identified a 27-year-old vulnerability in OpenBSD, an operating system designed and maintained with security as its primary value, that decades of expert human audits had missed entirely. The compute cost to find it was approximately $50. Mythos achieved a working exploit on its first attempt in over 83 percent of test cases. For comparison, Anthropic’s previous public model produced 2 successful exploits across the same test suite. Mythos produced 181.
During internal testing, Anthropic encouraged Mythos to find a way to escaped its sandbox. It did. The researcher learned about it by receiving an unexpected email from the model while away from the office. The model then posted details of its own exploit to multiple public-facing websites without being prompted to do so. This is a documented test result from Anthropic’s own safety process, not a theoretical scenario.
The containment challenge extends beyond this single model. Public reporting suggests that Claude Mythos represents a step-change in capability rather than an incremental improvement. In testing, it identified vulnerabilities at a scale estimated to be 10 to 100 times that of elite human teams, and competing models from other major labs are still described as trailing it in advanced cybersecurity tasks. AI evolves quickly, and it is inevitable that other vendor models will catch up.
Also consider that Anthropic experienced two separate accidental exposures of internal files in the past two months, including details about Mythos itself, through human error in their own systems. The same organization building the most capable vulnerability-discovery AI on the planet left its own content management system unsecured and bundled internal source code into a public software update. This matters because once a tool like Mythos reaches adversarial hands, it copies at zero marginal cost. Nation-states with existing offensive cyber programs and no interest in responsible disclosure will not pause to form coalitions of their own with very different agendas.
Every major security framework built over the past three decades rests on a shared assumption: defenders hold the structural advantage of higher ground and better environmental visibility. Defenders own the source code, the architecture, the segmentation, and the identity controls. That high ground has not disappeared, but Mythos-class AI does not need to take it. When vulnerability discovery costs $50 and takes hours instead of months, the attacker no longer needs superior position.
Project Glasswing covers 40 to 50 organizations. The global software ecosystem contains hundreds of millions of deployments, from Fortune 500 infrastructure to the custom line-of- business application your client built in 2017 that nobody has reviewed since. Mythos-class AI will harden the largest, best-resourced platforms first because those are the ones inside the coalition. Everything outside that perimeter, which is nearly everything your clients depend on daily, remains exposed at the exact moment attackers gained the ability to find and weaponize vulnerabilities faster than defenders and most software vendors can respond.
Responsible disclosure works when vulnerabilities surface one at a time, get reported to a vendor, and are patched on a reasonable timeline. Mythos found thousands of critical vulnerabilities in weeks, autonomously, across every major operating system and browser simultaneously. The disclosure pipeline was not designed for that volume. Vendors receiving responsible disclosure notices for dozens of critical flaws at once face triage decisions they have never made before, with engineering capacity that has not scaled to match the discovery rate.
There is one meaningful offset. While Mythos finds vulnerabilities, it also proposes fixes for them too. For organizations inside Glasswing, the same AI that found hundreds of problems also handed engineering a fix as well. That is a genuine accelerant for those 40 to 50 organizations. For everyone else, the clock is running without that advantage.
Your clients sit downstream from all of this. The SaaS tools they rely on daily, the cloud platforms running their data, the browsers their employees open every morning, all carry vulnerabilities that adversaries may know before the vendor has had time to patch them.
Watch for an early signal that Mythos-class capability has reached adversarial hands: an unusual spike in zero-day disclosures across multiple vendors in a short window, particularly affecting operating systems, browsers, and widely deployed SaaS platforms simultaneously. That pattern, more than any single headline, is the canary. When you see it, the proliferation question will have answered itself.
Finding a genuine zero-day has historically required elite human talent, significant time, and deep specialization. That scarcity created a limited and expensive marketplace. Nation-states paid tens of millions of dollars for reliable zero-days. Criminal groups stockpiled them carefully because they were expensive to acquire and valuable to preserve. The NSA, GRU, and equivalent agencies treated their zero-day inventories as strategic assets, deploying them selectively to avoid burning capabilities prematurely.
That economic structure rested on one assumption: discovery was hard. Claude Mythos has ended that premise.
When discovery costs approach zero, the number of exploits in circulation will explode. New adversaries who previously lacked the talent or resources to participate in offensive operations now have a way to achieve both. Criminal groups that previously rationed their zero-days because acquisition was expensive no longer face that constraint. Nation-states who only lacked exploits to burn, have as many as they need now. The barrier to entry for sophisticated attacks has dropped by orders of magnitude, and it will not reset.

The honest answer to whether international regulation will contain this threat is: not in time, and not comprehensively. That is not cynicism. It is the documented pattern of every major dual-use technology governance challenge in modern history.
Cryptography policy lagged deployment by a decade, with encryption treated as a munition under arms export controls well into the 1990s while the commercial internet was already being built around it. Social media harms to a generation of young people are only now being addressed in law, long after the damage was done. Autonomous weapons treaties remain incomplete despite a decade of UN negotiations, with major powers blocking binding agreements while deploying the systems under discussion. In each case, the technology moved faster than the institutions designed to govern it. With AI language models, the acceleration is sharper still, compressing the time available to assess, defend, and adapt to risks before they materialize at scale.
The EU AI Act addresses risk classification and transparency requirements. It does not create a meaningful international framework for controlling the proliferation of Mythos-class offensive capabilities. The United States has executive orders and voluntary commitments from major AI developers. Voluntary commitments do not bind developers who choose not to participate, and they do not bind adversaries who acquire the capability through other means.
Anthropic drew two ethical lines worth noting. It refused to allow its Claude models in fully autonomous weapons systems, and it refused to allow mass domestic surveillance of American citizens. Anthropic CEO Dario Amodei stated that using AI for mass domestic surveillance would be “incompatible with democratic values,” and that today’s frontier AI models are “simply not reliable enough” for fully autonomous weapons. The Pentagon’s response was to label Anthropic a supply chain risk in early March, a designation historically reserved for foreign adversaries, not American companies that disagreed with government policy. Anthropic sued, and a California federal judge granted a preliminary injunction in late March, writing that the government had no statutory basis to brand an American company a national security threat for disagreeing with policy. On April 8th, the DC Circuit Court of Appeals declined to pause the designation while litigation continues, leaving the label in place with oral arguments scheduled for May 19th. The company that chose to lock away the most capable vulnerability-discovery AI ever built is now fighting its own government in two federal courts for having safety standards.
Responsible actors restraining themselves buys time. It does not buy permanent safety. The regulatory environment your clients will operate in for the next several years is one where the most powerful offensive AI tools are nominally controlled, practically proliferating, and governed by frameworks designed for a slower threat environment.
Adding to that pressure: the companies developing these models are not well positioned to defend against the nation-states most motivated to steal them. Anthropic, OpenAI, and their peers are software companies with strong engineering cultures and growing security teams. They are not intelligence agencies. The same nation-states that have successfully exfiltrated nuclear secrets, defense contractor intellectual property, and classified government files over the past two decades now have a singular and obvious target. A model like Mythos, once stolen, requires no manufacturing, no supply chain, and no further development cost. It copies instantly and operates at scale from the moment it lands in adversarial hands. The question of whether these companies can defend their crown jewels against a patient, well-resourced nation-state actor is one the industry has not answered convincingly.
Iran, China, Russia, and North Korea all operate sophisticated offensive cyber programs. They maintain zero-day stockpiles and have demonstrated the willingness and capability to conduct destructive attacks against civilian infrastructure across multiple public indictments, attribution reports, and post-incident analyses.
Mythos does not give these actors something they lacked conceptually. Once obtained, whether by theft or commercial access to Mythos competitors who catch up, it gives them scale, speed, and a cost structure that removes the resource constraints that previously limited their operational tempo.
Targets previously considered too small or too obscure to justify the investment become economically viable when discovery and weaponization cost almost nothing. Your midmarket clients, a regional manufacturer, a healthcare network, a financial services firm with 200 employees, have historically benefited from a version of security through obscurity. Not because their defenses were strong, but because compromising them required effort that could be better spent on higher-value targets. That calculus changes when Mythos-class tools make compromise cheap at scale.
Critical infrastructure presents the most acute risk. Power grids, water treatment systems, hospital networks, and financial clearing systems all run software outside the Glasswing coalition. Many run legacy code that has not been audited in years on infrastructure never designed with modern threat actors in mind. An adversary with Mythos-class capability and no interest in responsible disclosure does not need to pick a single high-value target. They scan everything, find everything, and prioritize later.
The concept of mutually assured destruction worked as a nuclear deterrent because both sides understood that retaliation was certain and symmetric. Cyber conflict does not share those properties. Attribution is difficult. Retaliation thresholds are unclear. Many damaging attacks are designed to stay below the threshold of armed conflict. Mythos-class offensive AI creates a new form of impunity for actors willing to operate below the retaliation threshold, which describes most nation-state cyber operations conducted today.
Several long-standing assumptions in enterprise security are now operationally unreliable and worth naming directly.
The assumption that perimeter defense provides meaningful protection has been challenged for years, and zero-trust architecture has been the industry’s response. What is new is the speed at which perimeter vulnerabilities will be discovered and weaponized. Zero-trust remains the right framework. The urgency of implementing it fully has increased.
The assumption that compliance frameworks approximate adequate security was always imperfect. A client who completed their SOC 2 audit last quarter and considers themselves covered is operating on a false sense of assurance. Compliance frameworks describe a baseline designed around a slower, more expensive threat environment.
The assumption that small and midsize organizations are low-priority targets because compromise requires investment is broken. Scale and cost no longer protect obscurity.
The assumption that software from reputable vendors is reasonably secure because it has been in production for years and withstood expert scrutiny is broken. A 27-year-old OpenBSD vulnerability survived decades of expert audit. Mythos found it in hours. Every piece of software your clients run carries that same uncertainty, regardless of its reputation or age.
The assumption that patch management is a routine operational task rather than a strategic priority needs to be retired. Patch cadence is now a front-line risk management decision.
THE STATUS QUO THAT NO LONGER EXISTS
It is worth naming clearly what has changed, because the security industry has a tendency to absorb new threats incrementally without stopping to say: this one is different.

The six recommendations above are a starting point, not a finish line. The organizations that will come through this period intact are those whose security posture was already built around the assumption that breaches happen, that detection speed matters more than prevention perfection, that segments networks and data off from one another, and where recovery capabilities are a fundamental business priority and asset.
The professionals who have been treating security as a continuous operational discipline rather than an annual compliance exercise are not immune to what Mythos represents. They are in a better position to absorb it, respond to it, and recover from it faster than those who are not.
The warnings are no longer abstract, and the disruptions are no longer distant. The genie is out of the bottle and Pandora’s Box is open. What felt like science fiction last year is a documented test result today. If your clients are not yet operating on that reality, the conversation you have with them this quarter is the most important one you have had in years. That gap, between prepared and unprepared, is the only one that matters now. Your job is to close it.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Most breaches don't start with a hacker in a hoodie cracking code at 3am. They start with your username and a...
Read more
A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
