Positive
Swap negative phish testing for the positive, gamified training that’s more effective at reducing real-world risks.
Get a grip of your security awareness training with the one-of-a-kind platform that uses fun, positive engagement to deliver more effective results.



Swap negative phish testing for the positive, gamified training that’s more effective at reducing real-world risks.
Set your training program up and let it soar, with no daily logins, no manual sending, and no extra management time.
Personalize your security awareness training with your brand, your schedule and your relevant content.
CyberHoot’s free Dark Web Report can help you find out.
CyberHoot’s Autopilot platform runs your security awareness training program with minimal oversight and maximum engagement. Each power-up module is quick and easy to activate for an extra line of defense.
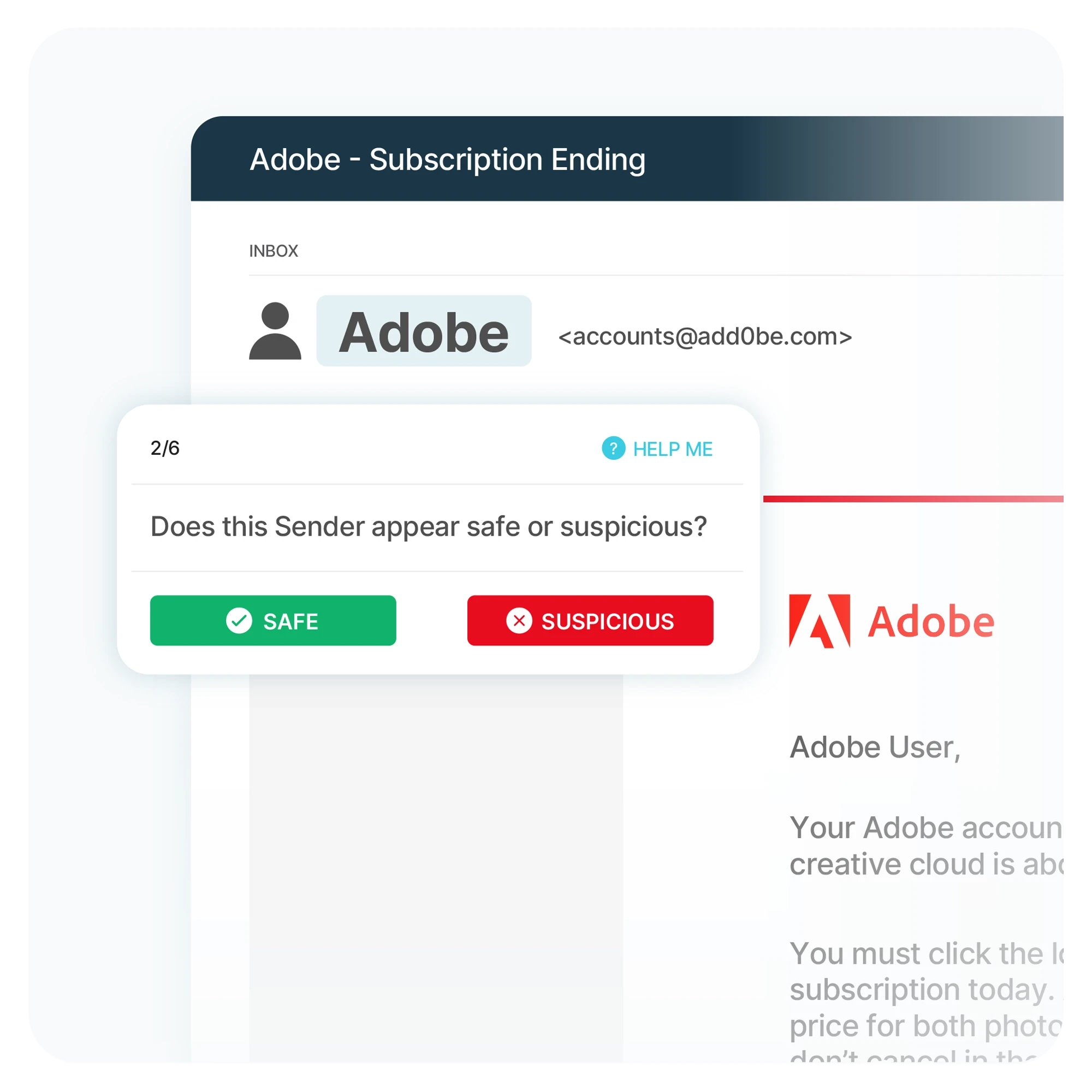
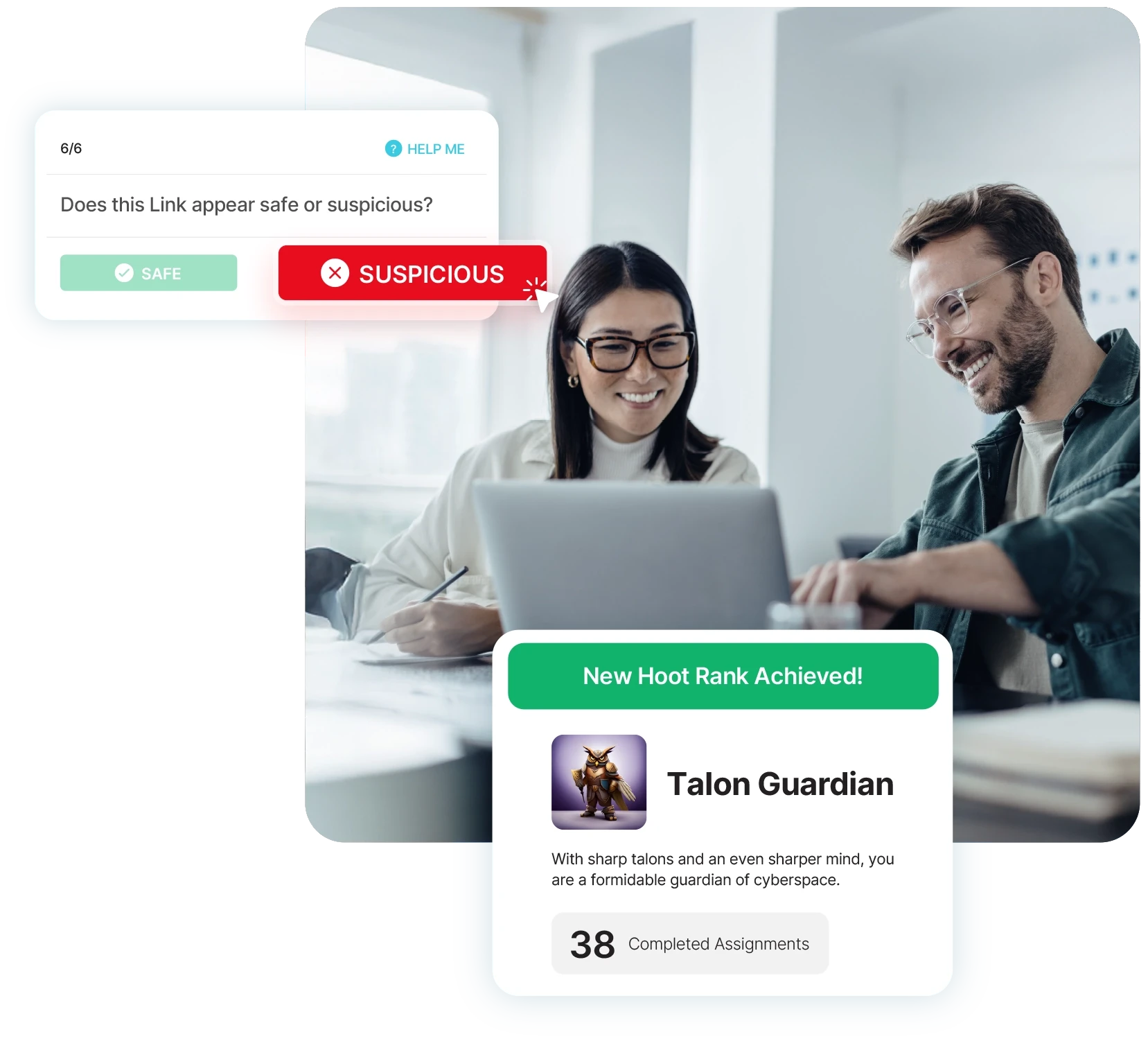
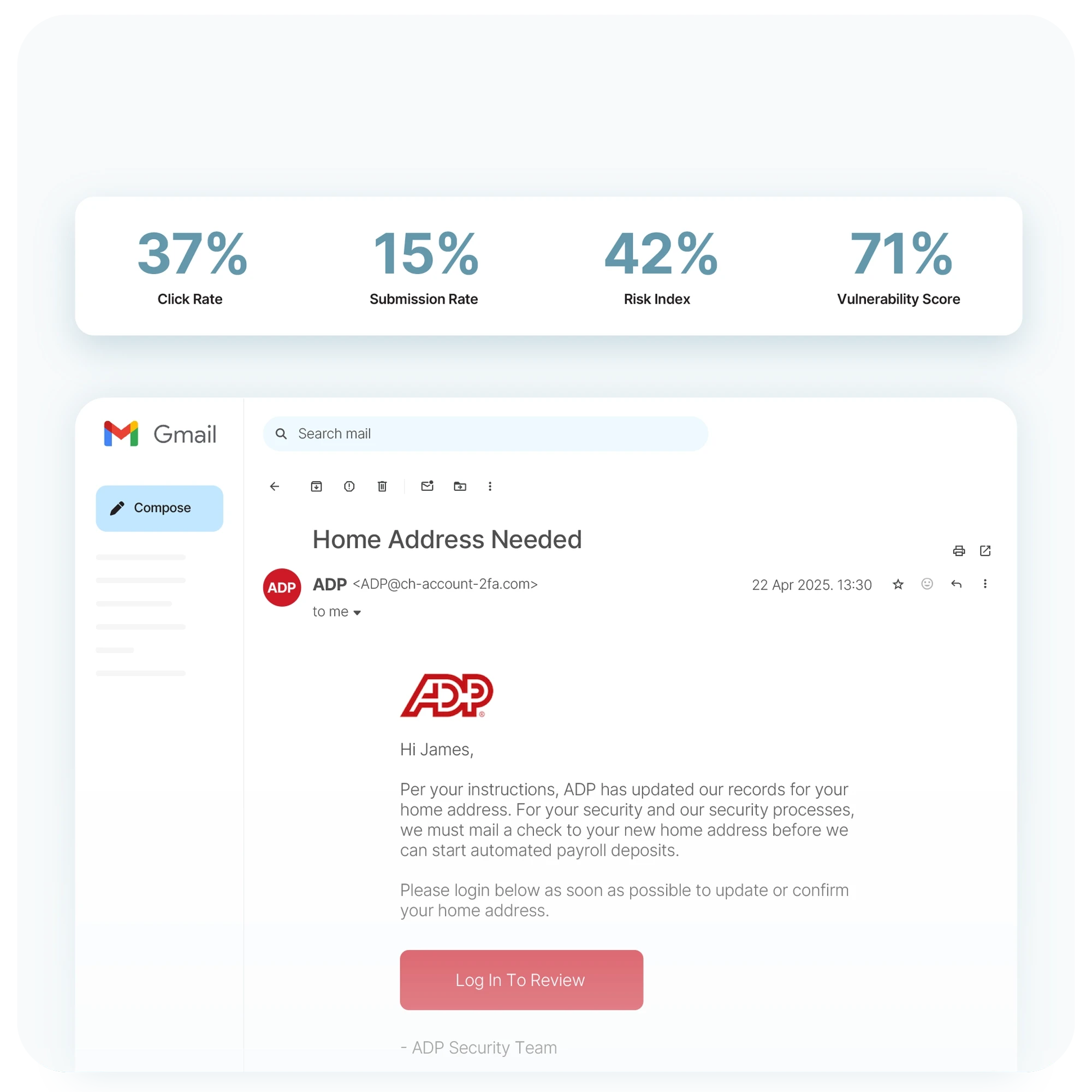
HootPhish doesn’t just test — it teaches.
Unique interactive training walks your users through real-world phishing scenarios, helping them identify the 6 key indicators of malicious emails.
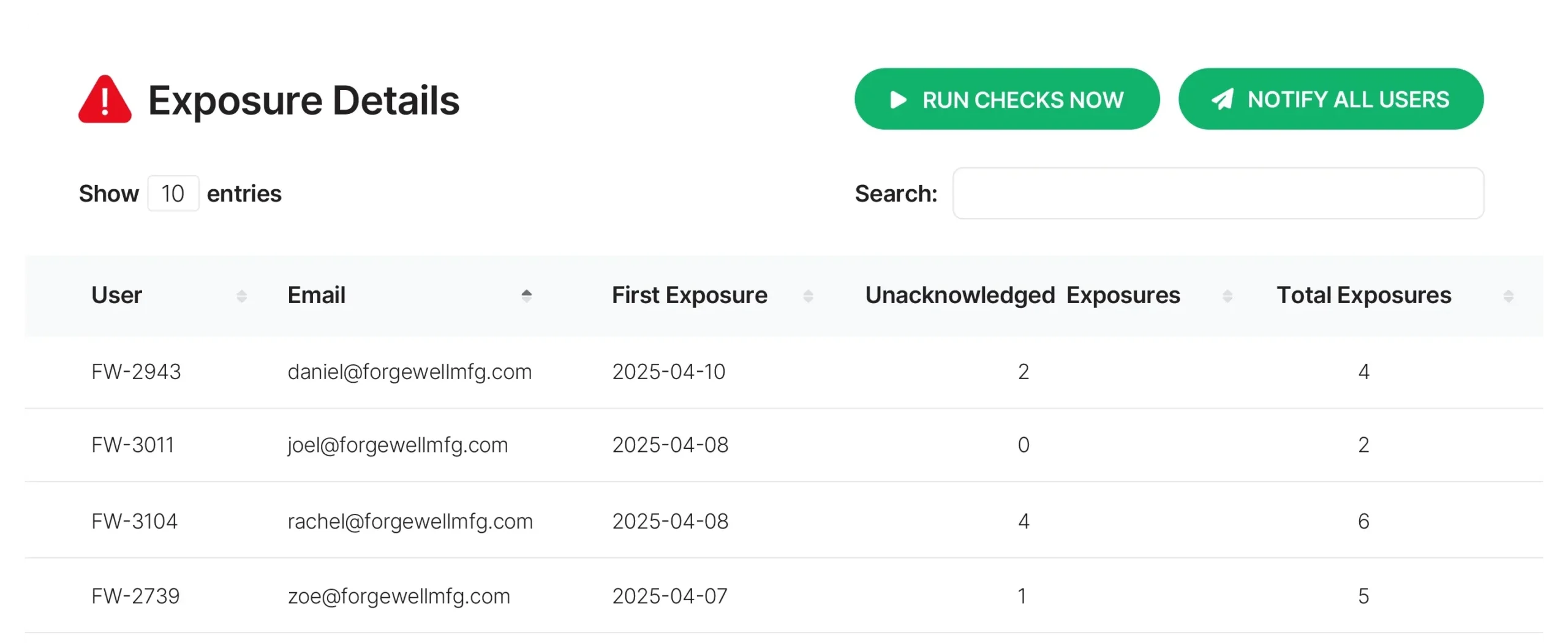
AttackPhish doesn’t just test — it scores.
Send highly relevant and realistic phishing emails that test your employees, then rank and rate individual and team performance to boost training completion rates.
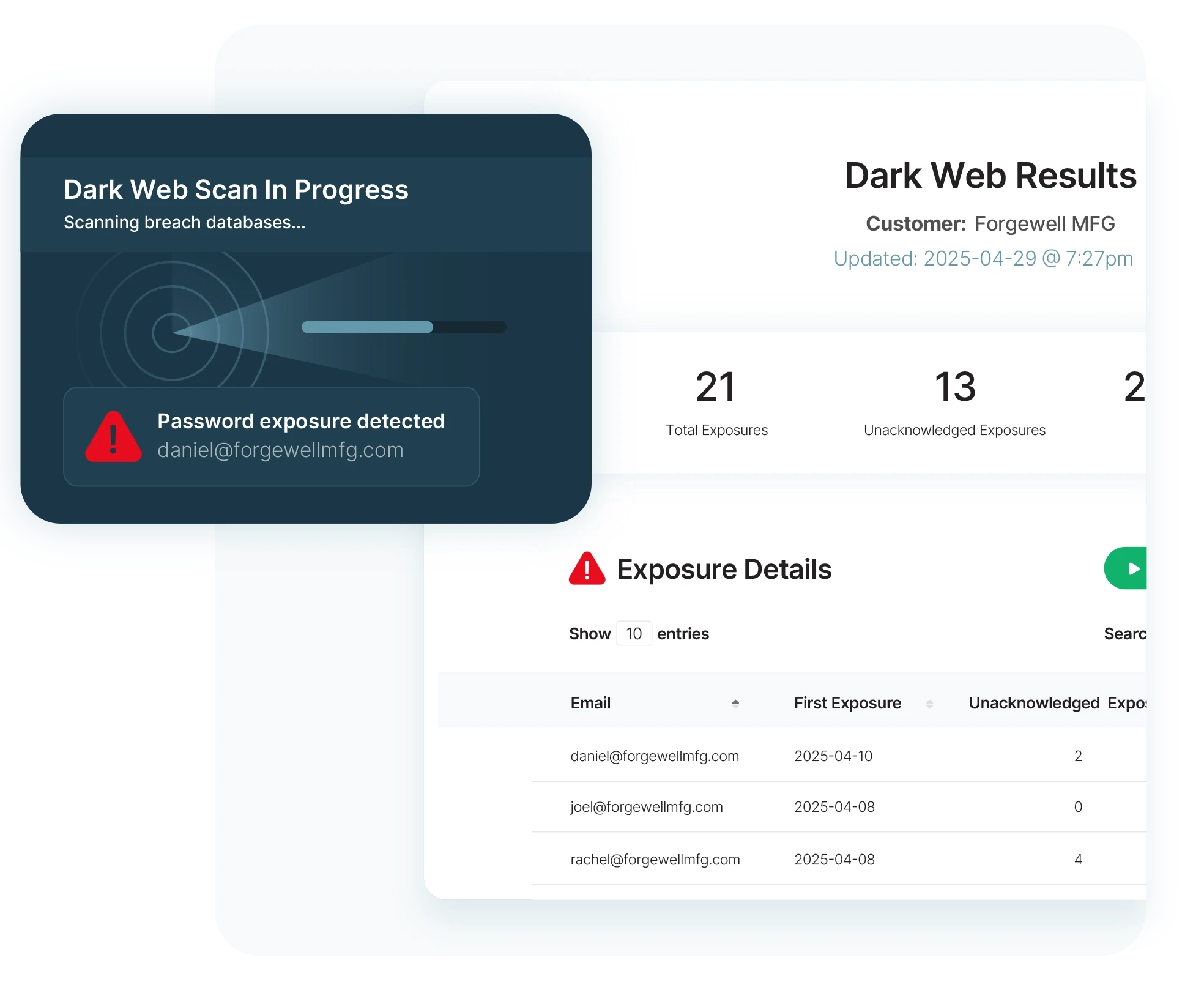
Dark Web Monitoring doesn’t just scan — it recommends.
Automated in-depth reports identify exposed personal data and prompt urgent actions to help protect compromised accounts.
CyberHoot integrates effortlessly with your existing tech stack – including EntraID and Google Workspace – to make security awareness training simple.



CyberHoot’s positive training approach adapts to your environment, your users, and your needs. Get powerful security awareness tailored to your organization.
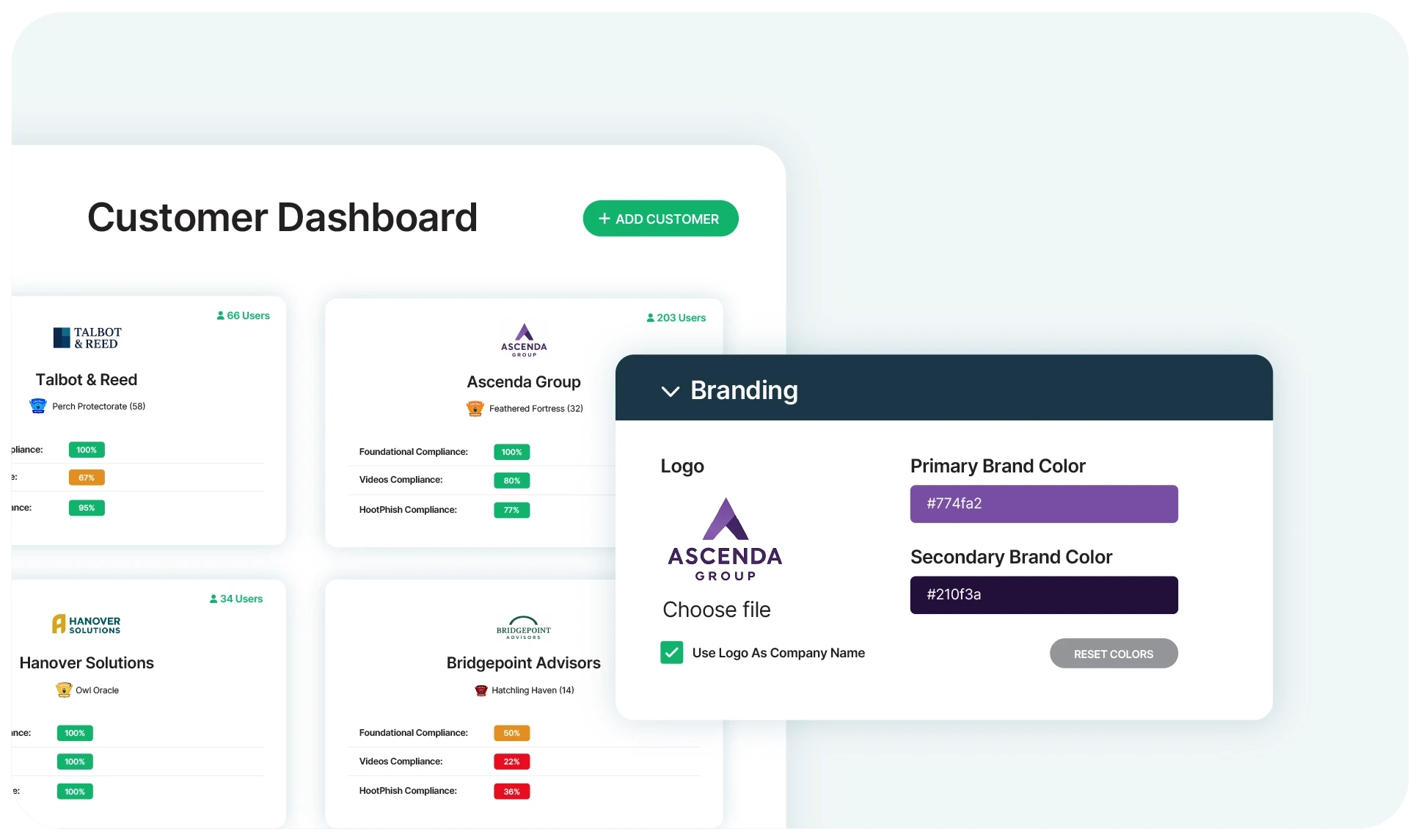
Swoop in with the hands-off, multi-tenancy white-labelled solution that protects your clients and your time.
Learn more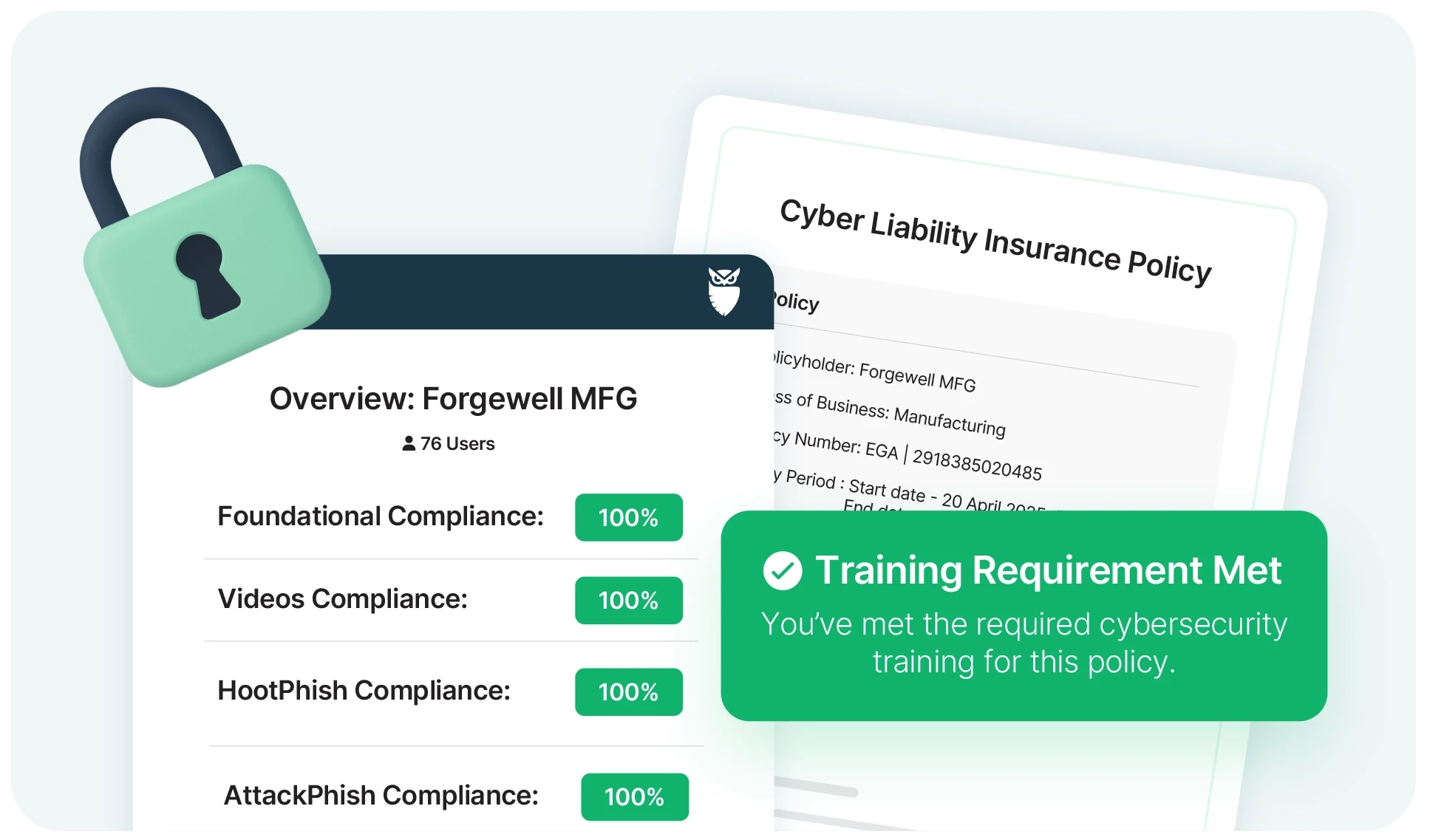
Meet cyber insurance requirements and turn your employees from a potential weak link to a strong asset.
Learn more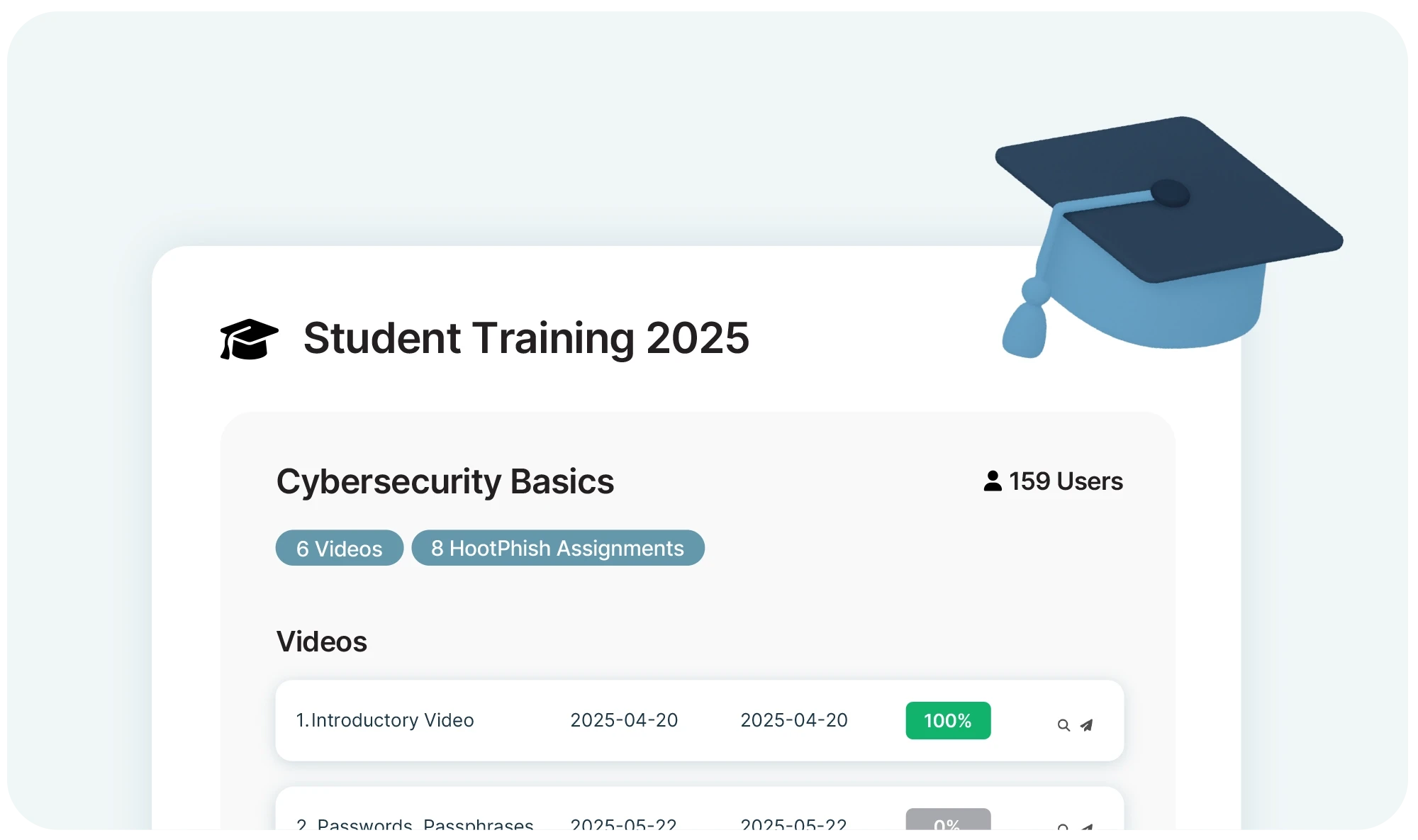
Get customized training for staff and students to help keep your institution’s data safe and secure.
Learn more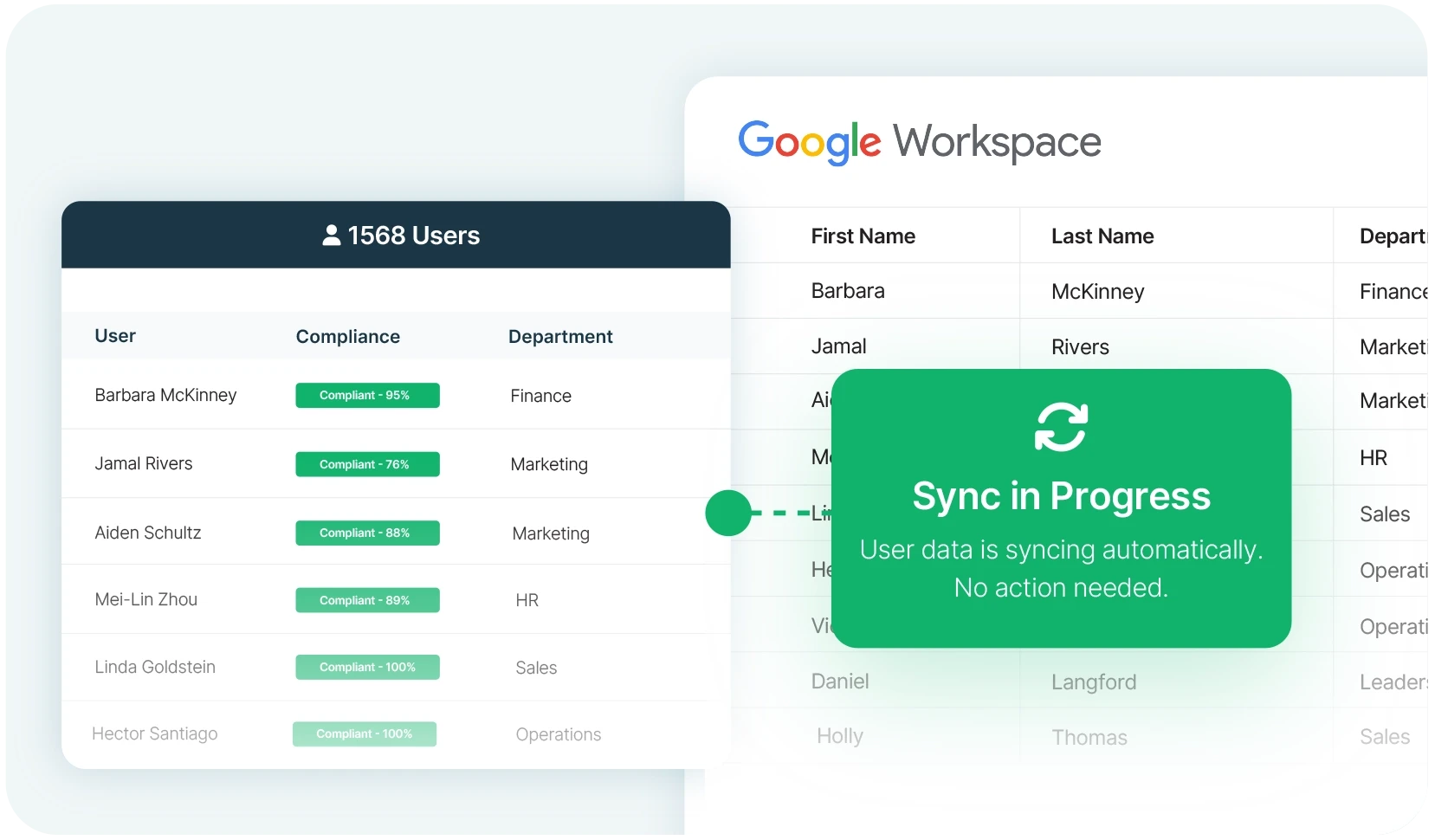
Scale cyber security training and testing across your organization, fully integrated with your ecosystem.
Learn more






Get sharper eyes on human risks, with the positive approach that beats traditional phish testing.
