"The ease of setup and use for both administrators and users was immediately apparent. The automated training and phishing awareness features are major time savers for HR and IT teams”
Image Source A vulnerability is a characteristic or specific weakness that renders an organization...
Read more
An Allow list, also known as a Permit List or (deprecated: White List), is a list of...
Read more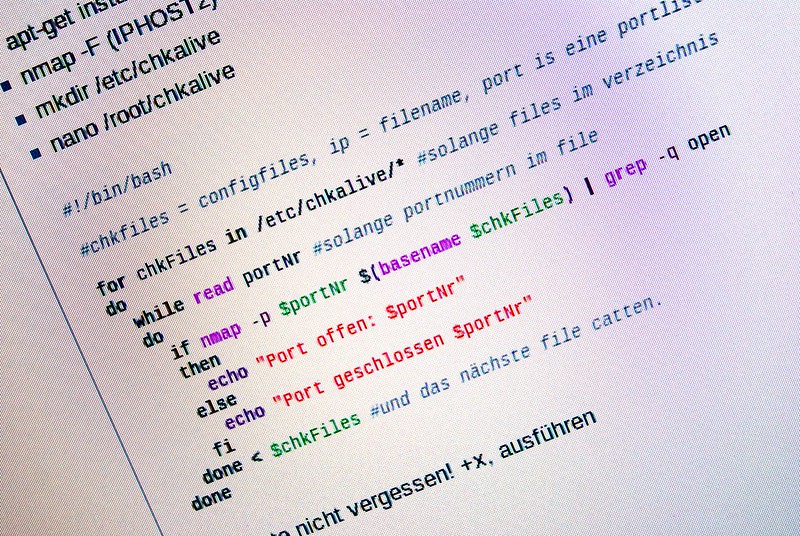
Image Source A Work Factor is an estimate of the effort or time needed by a potential adversary, with...
Read more
Image Source A White Team is a group responsible for refereeing an engagement between a Red Team...
Read more
Compromised Credentials occurs when an unsuspecting user's login username and password are in the possession...
Read more
This past Thanksgiving weekend, 110 healthcare facilities were infected by a ransomware attack on their IT...
Read more
Who is most likely to fall victim to Cyber Monday phishing scams? People who don't know about phishing scams,...
Read more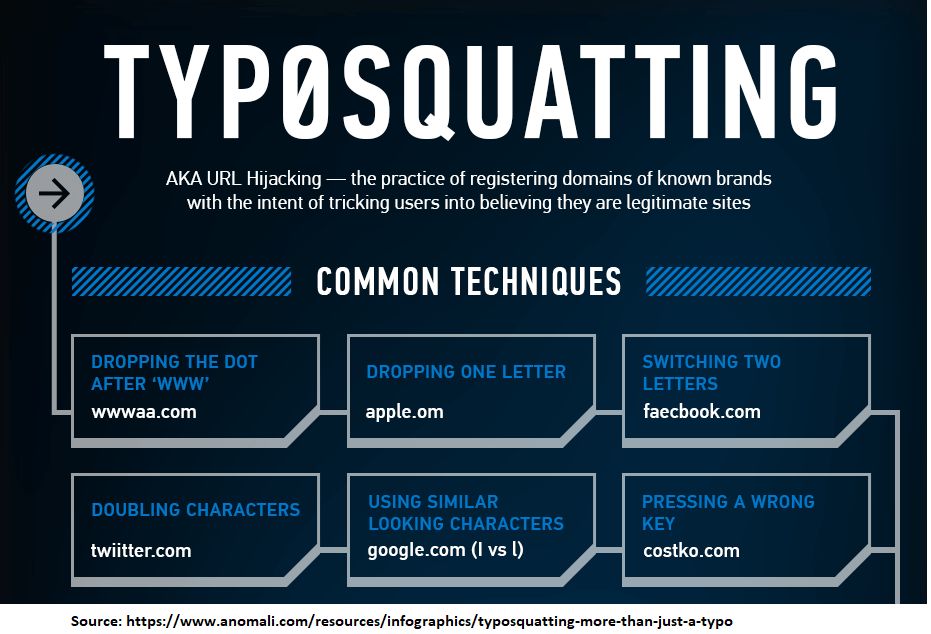
Typosquatting is also called URL hijacking. It is a form of cybersquatting which relies on mistakes such as...
Read more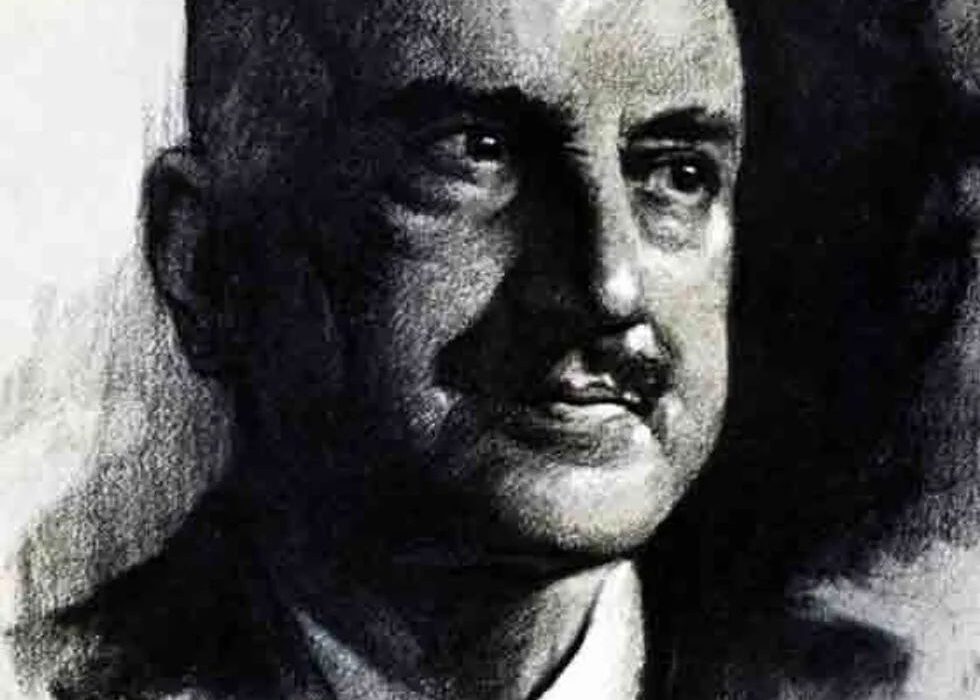
George Santayana (Sketch artist: Samuel Johnson Woolf) "Those who cannot remember the past are condemned to...
Read more
The FBI issued a stern warning in February 2019. They witnessed multiple Managed Service Providers...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
