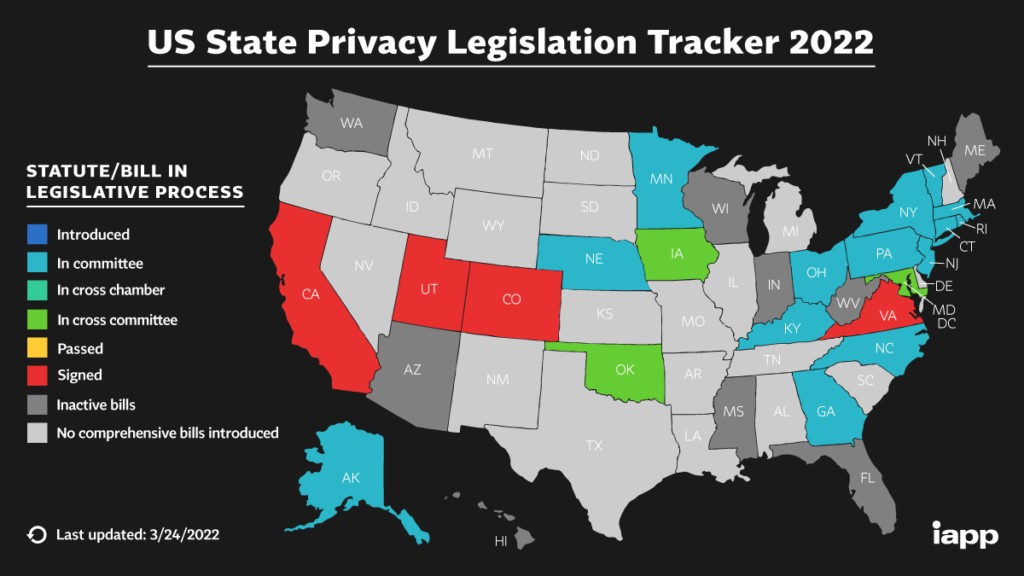
Privacy legislation has expanded significantly in the last two years with the publication and enforcement of the EU’s General Data Privacy Regulation (GDPR). In Jan. 2020, the California Consumer Privacy Act (CCPA) will go into effect, with similar requirements to GDPR, in CA. Other states including Texas, New York, Washington, and Massachusetts are following suite. EU and CA privacy legislation attempts to protect our private data by granting certain rights. These rights allow one to manage the data businesses keep on us through “Data Privacy Requests”. These requests can include but are not limited to the right to have businesses:
- forget my private data;
- correct my private data;
- prohibit my private data from being sold; and importantly,
- request a business provide me my private data.
Unfortunately, businesses have not prepared properly for these requests. World wide, businesses are scrambling to accommodate GDPR data privacy requests being made by EU residents. US businesses with private data on Californians are hurrying to build processes to accommodate data privacy requests from CA residents beginning January 1st, 2020.
Wouldn’t it be ironic if the next wave of privacy breaches stemmed from data privacy requests made by hackers under these legislative acts? This is the very problem CyberHoot sees with these acts. Businesses have not yet built robust, multi-factor “Data privacy request” processes that verify the identity of each requester!
A Horse named “Black Irony” has Left the Stable
Surprise, surprise, a British researcher name James Pavur, reported in this Black Hat briefing in Aug. 2019, that after making 150 “data privacy requests” for his wife’s private data, businesses sent him her:
- Social Security Number;
- current and previous home addresses;
- credit card numbers;
- School grades;
- Hotel Logs; and
- whether she used certain dating websites or not.
Importantly, Pavur did not forge any documents, signatures or email addresses. He used his own credentials, signature, and email account in every case to request these items. Businesses simply did not verify his identity. Now, imaging what a hacker who forges signatures, documents, and breaks into your email account could do? CyberHoot has some predictions for you.
Privacy Regulation Predictions/Suggestions for Businesses:
- Hackers will exploit privacy regulations through weak verification mechanisms to steal the very private data these acts are meant to protect.
- While CCPA is aware of verification challenges and promises to publish clarification on what constitutes verifiable requests through CA’s Attorney General (AG), business cannot afford to wait. Businesses should create their own verification measures, possibly following measures adopted by Banking (see below) to prepare in time for January 1st, 2020.
- Banks have the verification process figured out. When CyberHoot calls its bank, the IVR asks for our 16 digit card number just to speak to an agent. The Bank agent then sends a 4 to 6 digit code to CyberHoot’s mobile device to require a second factor to verify our identity (something we know and something we have).
- Businesses would be wise to adopt similar two-factor authentication measures for all privacy data requests.
- Some businesses CyberHoot consults with don’t collect the requisite data (Account numbers, Email addresses, and/or Mobile phone numbers) to properly verify an individuals identity. Hopefully the CA AG will exempt these companies from complying with data privacy requests rather than force them to collect more of our private data just to comply with these data privacy requests.
What might Private Citizens do to Protect themselves?
- Contact businesses that have your critical and sensitive data and ask how they will verify your identity for such requests. Tell them that email is not enough and that they need to identify you with two-factors just like banks do.
- While extreme, ask yourself whether it’s time to delete your Search and Social Media data using existing tools and processes.
CyberHoot is not suggesting Google and Facebook will be easily fooled into giving your private data away. However, other companies who have your data are not yet prepared to handle these requests. CyberHoot challenges businesses to build secure verification processes before hackers exploit you in this novel and horribly ironic way.
Author, Craig, Co-Founder – CyberHoot
